السلام عليكم و رحمة الله تعالى و بركاته
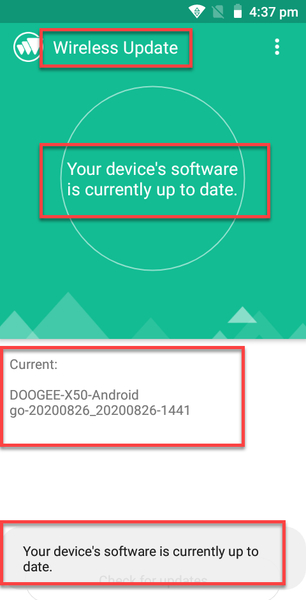
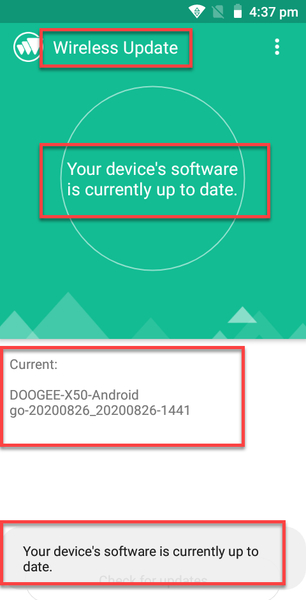
تم بحمد الله سحب فلاشة هاتف DOOGEE X50 أندرويد 8.1.0 تاريخ 20200826 معالج MT6580 دونجل CM2 واجهة MT2 + فلاشة فول دامب بصيغة سكاتر ميراكل بوكس

CM2 DONGLE
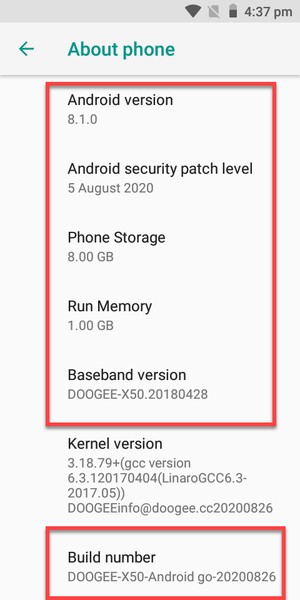
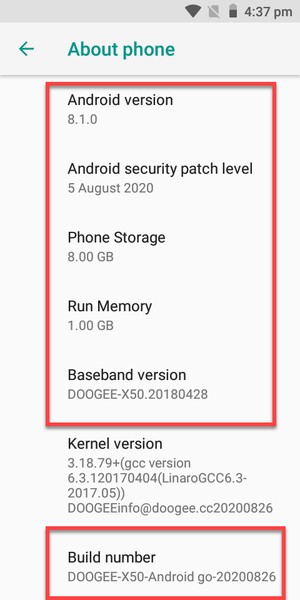
انفو الهاتف
تم بحمد الله سحب فلاشة هاتف DOOGEE X50 أندرويد 8.1.0 تاريخ 20200826 معالج MT6580 دونجل CM2 واجهة MT2 + فلاشة فول دامب بصيغة سكاتر ميراكل بوكس

CM2 DONGLE
انفو الهاتف
كود:
[LEFT][SIZE=4][COLOR=#0000FF]Operation : Identify [ v2.21 ][/COLOR][/SIZE]
Mode : FLASH
Boot done!
Patch Level : O11019
Display ID : [SIZE=4][COLOR=#0000FF]DOOGEE-X50-Android go-20200826[/COLOR][/SIZE]
Ver. CodeName : REL
Ver. Release : 8.1.0
Sec. Patch : 2020-08-05
Build Time : 26.08.2020
Product Model : X50
Product Brand : [SIZE=4][COLOR=#0000FF]DOOGEE[/COLOR][/SIZE]
Product Name : X50
Product Device : [SIZE=4][COLOR=#0000FF]X50[/COLOR][/SIZE]
Product Manfct : Vanzo
Product Info : X50
Product Board : wd359bf
Board Platform : [SIZE=4][COLOR=#0000FF]mt6580[/COLOR][/SIZE]
USERDATA : FILESYSTEM : F2FS with FDE ( Full Disk Encryption ***)
Done!
Elapsed: 00:00:24[/LEFT]بيانات سحب الفلاشة
كود:
[LEFT][SIZE=4][COLOR=#0000FF]Operation : Read Firmware [ v2.21 ][/COLOR][/SIZE]
ExtSparse : Enabled
ForceRead : Disabled
[SIZE=4][COLOR=#0000FF]MT6580__Vanzo__X50__8.1.0__DOOGEE-X50-Android_go-20200826__O11019__X50[/COLOR][/SIZE]
Read : preloader.bin
Read : proinfo.img
Read : nvram.bin
Read : lk.bin
Read : boot.img
Read : recovery.img
Read : logo.bin
Read : odmdtbo.img
Read : vendor.img
ExtSparse : Compression ratio : 68%
Read : tz.img
Read : secro.img
Read : system.img
ExtSparse : Compression ratio : 30%
Read : cache.img
Read : userdata.img
FW Size : [SIZE=4][COLOR=#0000FF]1.09 GB[/COLOR][/SIZE]
Android Info saved : _Android_info.txt
Scatter : MT6580_Android_scatter.txt
Saved to : D:\DOOGEE X50 8.1.0 20191205 CM2MT2\MT6580__Vanzo__[SIZE=4][COLOR=#0000FF]X50__8.1.0__DOOGEE-X50-Android_go-20200826[/COLOR][/SIZE]__O11019__X50\
Done!
Elapsed: 00:06:54[/LEFT]فيدو يوضح عملية السحب
[video=youtube_share;lx0hWPMSNAk]https://youtu.be/lx0hWPMSNAk[/video]

--------------------------------------------------------------------------------------------
MIRACLE BOX
انفو الهاتف
[video=youtube_share;lx0hWPMSNAk]https://youtu.be/lx0hWPMSNAk[/video]

--------------------------------------------------------------------------------------------
MIRACLE BOX
انفو الهاتف
كود:
[LEFT] 1. Power Off Phone , Remove Battery, Insert Battery Back
2. Insert USB cable. In some cases Required Hold BootKey
3. Use Miracle Boot Key In cases Boot key not Find
4. Battery Should be Charged more then 50%
Waiting for USB Port...
Set MediaTek PreLoader USB VCOM (Android) (COM90)
Connecting to Phone,Wait..
Connected to Phone.
CPU: [SIZE=4][COLOR=#0000FF]MT6580[/COLOR][/SIZE] SW:0000 Ver: CA00
Downloading Boot8 ...
EMMC Size: 0x01D2000000
Flash Type: EMMC
INT/EXT RAM Size: 0x20000/0x40000000
Reading infr(EMMC)...
BT_ADDR:1ACC460000C4
WIFI MAC:000000000000
IMEI1:35************0
IMEI2:35************8
id:[SIZE=4][COLOR=#0000FF]DOOGEE-X50-Android go-20200826[/COLOR][/SIZE]
version:[SIZE=4][COLOR=#0000FF]8.1.0[/COLOR][/SIZE]
model:[SIZE=4][COLOR=#0000FF]X50[/COLOR][/SIZE]
brand:[SIZE=4][COLOR=#0000FF]DOOGEE[/COLOR][/SIZE]
manufacturer:Vanzo
>>Done.[/LEFT]بيانات سحب الفلاسة
كود:
[LEFT] 1. Power Off Phone , Remove Battery, Insert Battery Back
2. Insert USB cable. In some cases Required Hold BootKey
3. Use Miracle Boot Key In cases Boot key not Find
4. Battery Should be Charged more then 50%
Waiting for USB Port...
Set MediaTek PreLoader USB VCOM (Android) (COM90)
Connecting to Phone,Wait..
Connected to Phone.
CPU: [SIZE=4][COLOR=#0000FF]MT6580[/COLOR][/SIZE] SW:0000 Ver: CA00
Downloading Boot8 ...
EMMC Size: 0x01D2000000
Flash Type: EMMC
INT/EXT RAM Size: 0x20000/0x40000000
Reading preloader...
Reading pgpt...
Reading proinfo...
Reading nvram...
Reading protect1...
Reading protect2...
Reading seccfg...
Reading lk...
Reading lk2...
Reading boot...
Reading recovery...
Reading para...
Reading logo...
Reading odmdtbo...
Reading expdb...
Reading vendor...
Reading frp...
Reading tee1...
Reading tee2...
Reading nvdata...
Reading metadata...
Reading oemkeystore...
Reading secro...
Reading keystore...
Reading system...
Reading cache...
[SIZE=4][COLOR=#0000FF]Saving as scatter file[/COLOR][/SIZE]...
>>Done![/LEFT]
