تثبيت التطبيق
How to install the app on iOS
Follow along with the video below to see how to install our site as a web app on your home screen.
ملاحظة: This feature may not be available in some browsers.
أنت تستخدم أحد المتصفحات القديمة. قد لا يتم عرض هذا الموقع أو المواقع الأخرى بشكل صحيح.
يجب عليك ترقية متصفحك أو استخدام أحد المتصفحات البديلة.
يجب عليك ترقية متصفحك أو استخدام أحد المتصفحات البديلة.
تجارب الأعضاء الناجحة فى تصليح و تفليش و فك شفرات الأجهزة على Hydra Dongle
- بادئ الموضوع DZ-Djamel-GSM
- تاريخ البدء
mouh@med
عضو أساسي
- إنضم
- 12 سبتمبر 2012
- المشاركات
- 776
- مستوى التفاعل
- 540
- النقاط
- 93
رد: تجارب الأعضاء الناجحة فى تصليح و تفليش و فك شفرات الأجهزة على Hydra Dongle
Redmi Note 7 Mi Account remove + FRP Remove
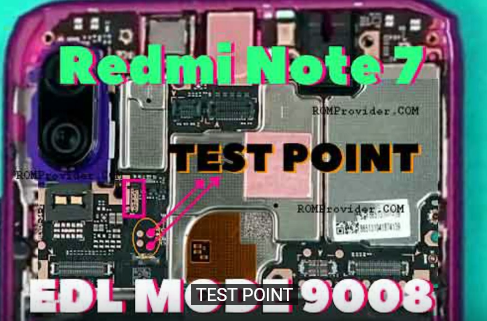
بدون بطارية .. نوصل نقطتي TP لمدة 5 إلى 10 ثواني قبل توصيل الكابل ... ثم نقوم بتبويت الجهاز حتى نتجنب مشكل
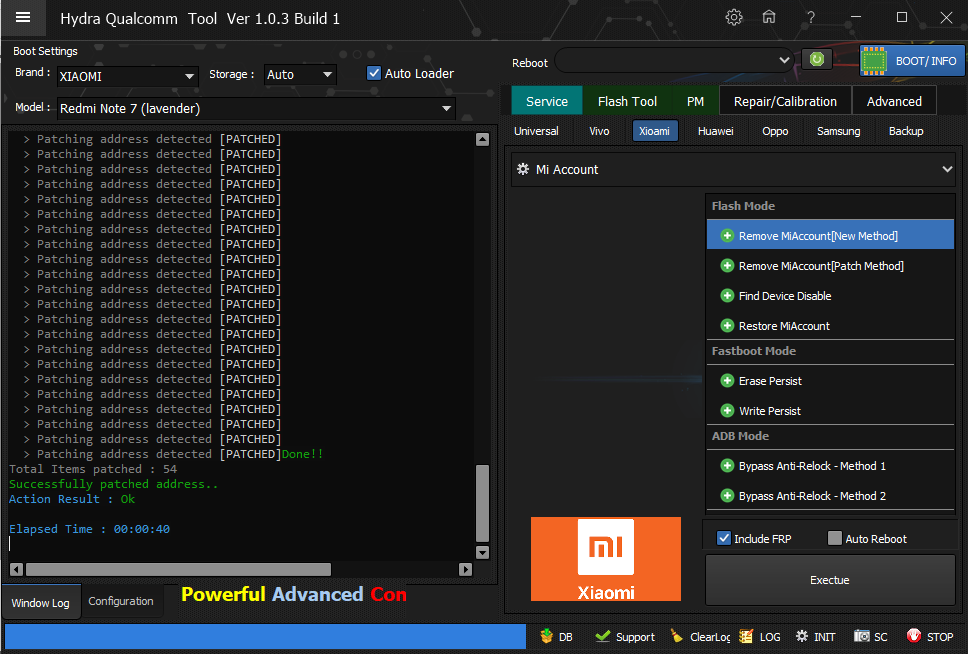
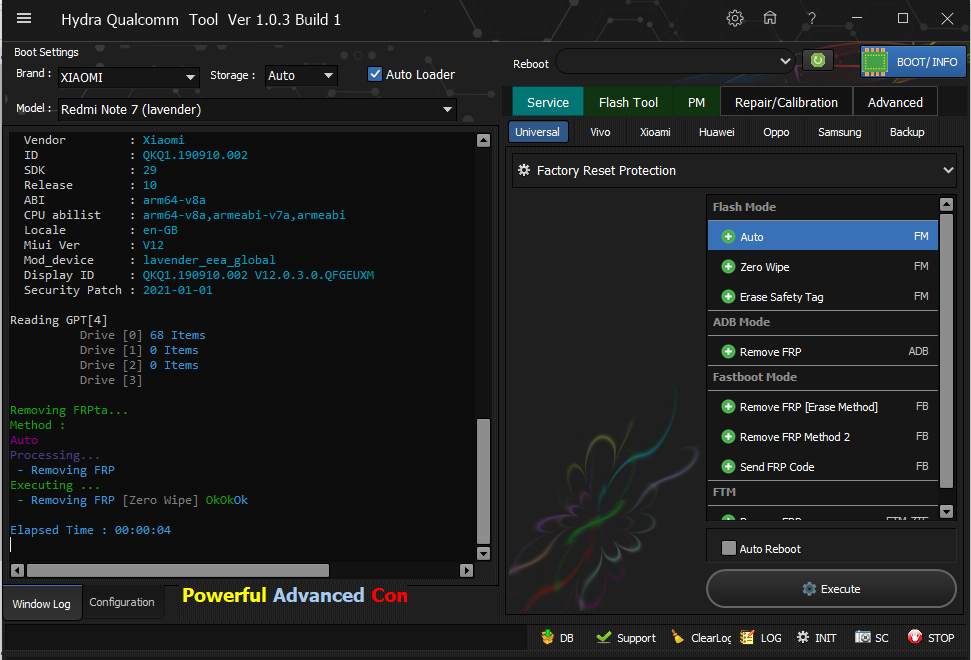
Redmi Note 7 Mi Account remove + FRP Remove
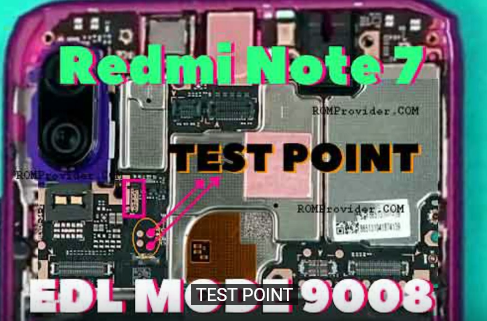
بدون بطارية .. نوصل نقطتي TP لمدة 5 إلى 10 ثواني قبل توصيل الكابل ... ثم نقوم بتبويت الجهاز حتى نتجنب مشكل
كود:
Signature @256bytes Authentication.... Denied..
Signature Verification Failed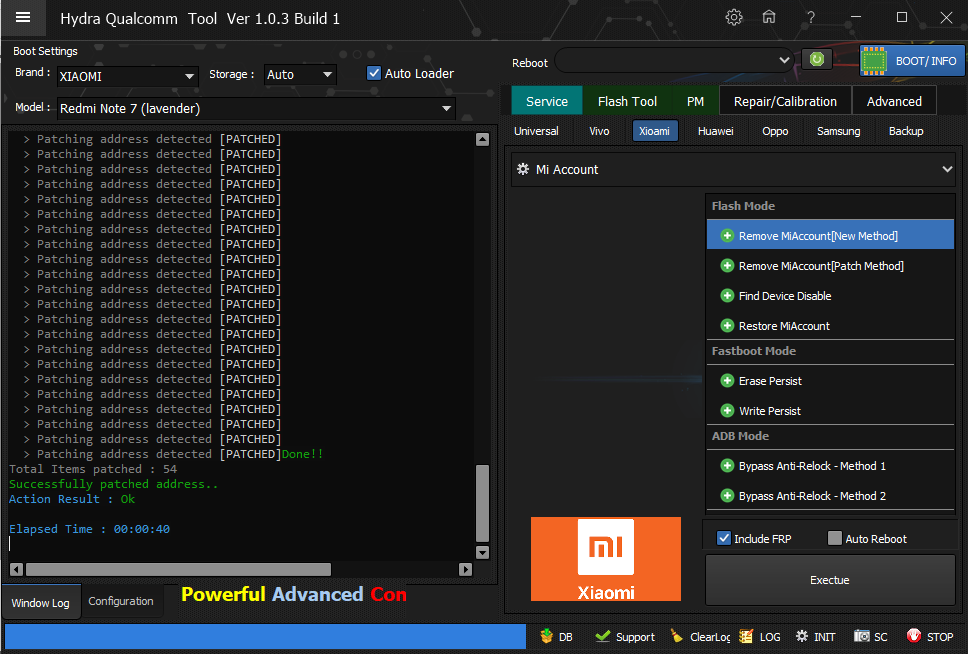
كود:
PreOperation Configuration
Brand : XIAOMI Model : Redmi Note 7 (lavender) Storage : Auto
Loader: mi_2_9.elf
Port : Auto
Searching for Qualcomm 9008 Device...Found
FriendlyName :Qualcomm HS-USB QDLoader 9008 (COM84)
SymbolicName :\??\USB#VID_05C6&PID_9008#6&186afa3&0&3#{a5dcbf10-6530-11d2-901f-00c04fb951ed}
Driver Ver :07/08/2015,2.1.2.0
Getting device info..Ok
Device MODE : Firehose
Connecting to Firehose...
Ping...... Ok
Configuration......
Identifying Chip....
Ok
Chip Configuration :
MemoryName : eMMC
MaxPayloadSizeToTargetInBytes : 1048576
MaxPayloadSizeToTargetInBytesSupported : 1048576
MaxPayloadSizeFromTargetInBytes : 4096
MaxXMLSizeInBytes : 4096
TargetName : MSM8996
Version : 1
DateTime : Aug 2 2018 - 22:27:53
*** STORAGE DEVICE INFO ***
Memory Type : eMMC
Block Size in Bytes : 512
Page Size : 512
Manufacturer ID : 19
Serial Number : 157875973
Firmware Version : 4
Product Name : S0J9K8
Physical Partitions : 4
Total Logical Blocks:
Drive [0] 122142720[58.242 GB]
Drive [1] 8192[4 MB]
Drive [2] 8192[4 MB]
Drive [3] 32768[16 MB]
Protocol : Universal
Running : Ok
Reading GPT[4]
Drive [0] 68 Items
Drive [1] 0 Items
Drive [2] 0 Items
Drive [3]
Phone Information......
Vendor : Xiaomi
ID : QKQ1.190910.002
SDK : 29
Release : 10
ABI : arm64-v8a
CPU abilist : arm64-v8a,armeabi-v7a,armeabi
Locale : en-GB
Miui Ver : V12
Mod_device : lavender_eea_global
Display ID : QKQ1.190910.002 V12.0.3.0.QFGEUXM
Security Patch : 2021-01-01
Processing Remove MiAccount[New Method]....
Backing up Partition for safety...Ok
Scanning Patching address...
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]
> Patching address detected [PATCHED]Done!!
Total Items patched : 54
Successfully patched address..
Action Result : Ok
Elapsed Time : 00:00:40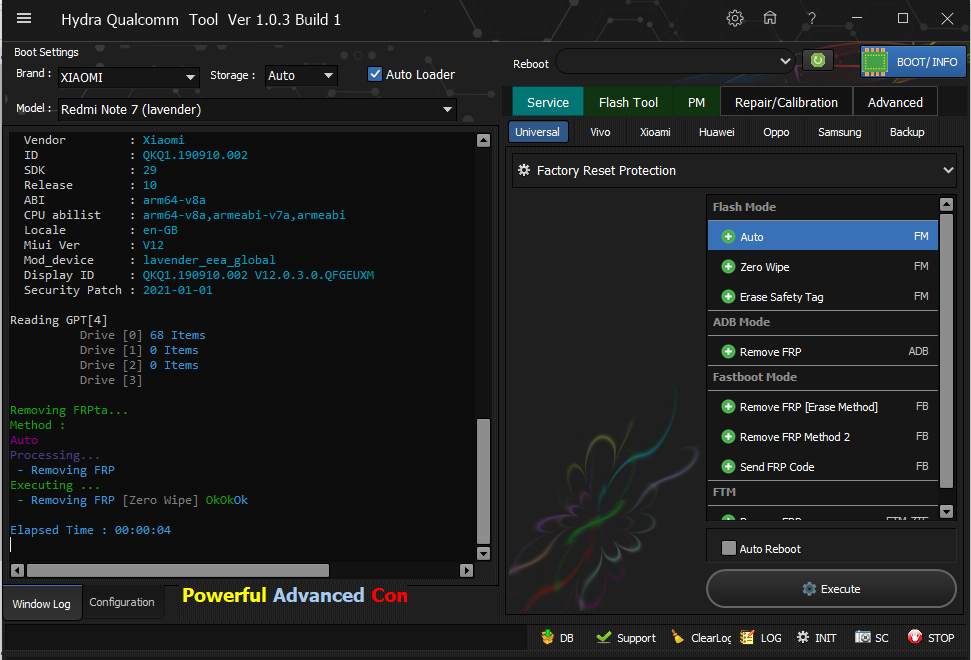
كود:
PreOperation Configuration
Brand : XIAOMI Model : Redmi Note 7 (lavender) Storage : Auto
Loader: mi_2_9.elf
Port : Auto
Searching for Qualcomm 9008 Device...Found
FriendlyName :Qualcomm HS-USB QDLoader 9008 (COM86)
SymbolicName :\??\USB#VID_05C6&PID_9008#6&2953c98d&0&4#{a5dcbf10-6530-11d2-901f-00c04fb951ed}
Driver Ver :07/08/2015,2.1.2.0
Getting device info..Ok
Device MODE : Firehose
Connecting to Firehose...
Ping...... Ok
Configuration......
Identifying Chip....
Ok
Chip Configuration :
MemoryName : eMMC
MaxPayloadSizeToTargetInBytes : 1048576
MaxPayloadSizeToTargetInBytesSupported : 1048576
MaxPayloadSizeFromTargetInBytes : 4096
MaxXMLSizeInBytes : 4096
TargetName : MSM8996
Version : 1
DateTime : Aug 2 2018 - 22:27:53
*** STORAGE DEVICE INFO ***
Memory Type : eMMC
Block Size in Bytes : 512
Page Size : 512
Manufacturer ID : 19
Serial Number : 157875973
Firmware Version : 4
Product Name : S0J9K8
Physical Partitions : 4
Total Logical Blocks:
Drive [0] 122142720[58.242 GB]
Drive [1] 8192[4 MB]
Drive [2] 8192[4 MB]
Drive [3] 32768[16 MB]
Protocol : Universal
Running : Ok
Phone Information......
Vendor : Xiaomi
ID : QKQ1.190910.002
SDK : 29
Release : 10
ABI : arm64-v8a
CPU abilist : arm64-v8a,armeabi-v7a,armeabi
Locale : en-GB
Miui Ver : V12
Mod_device : lavender_eea_global
Display ID : QKQ1.190910.002 V12.0.3.0.QFGEUXM
Security Patch : 2021-01-01
Reading GPT[4]
Drive [0] 68 Items
Drive [1] 0 Items
Drive [2] 0 Items
Drive [3]
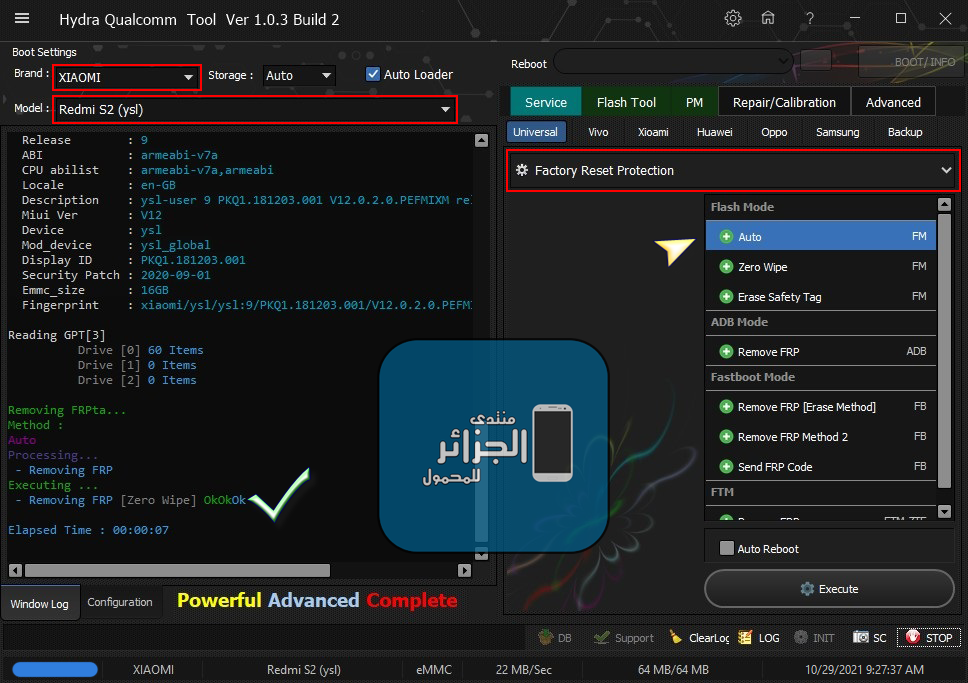
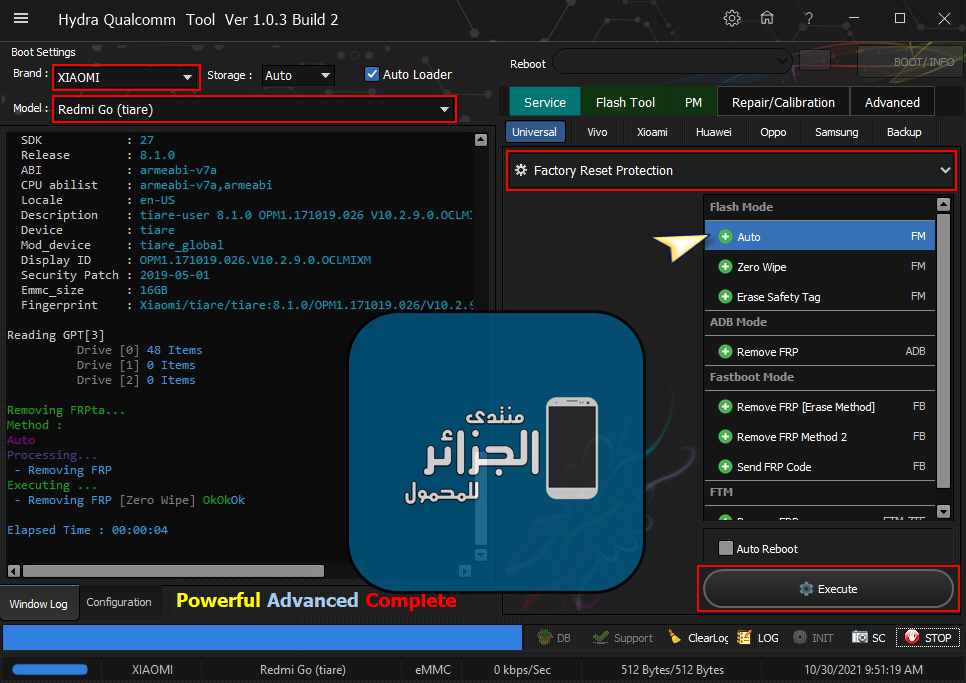
Removing FRPta...
Method :
Auto
Processing...
- Removing FRP
Executing ...
- Removing FRP [Zero Wipe] OkOkOk
Elapsed Time : 00:00:04رد: تجارب الأعضاء الناجحة فى تصليح و تفليش و فك شفرات الأجهزة على Hydra Dongle
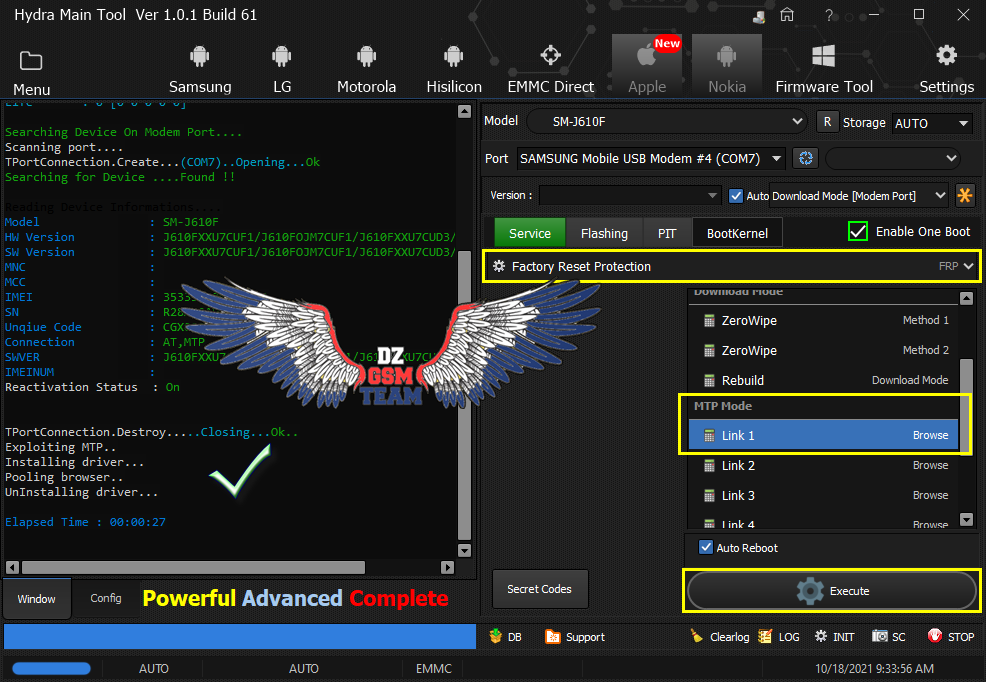
Samsung Galaxy J6 Plus (SM-J610F) Android 10 U7
FRP Bypass MTP Mode
[video=youtube;hRqU6lFb-8U]https://www.youtube.com/watch?v=hRqU6lFb-8U&ab_channel=SmartPhoneRepair[/video]
Samsung Galaxy J6 Plus (SM-J610F) Android 10 U7
FRP Bypass MTP Mode
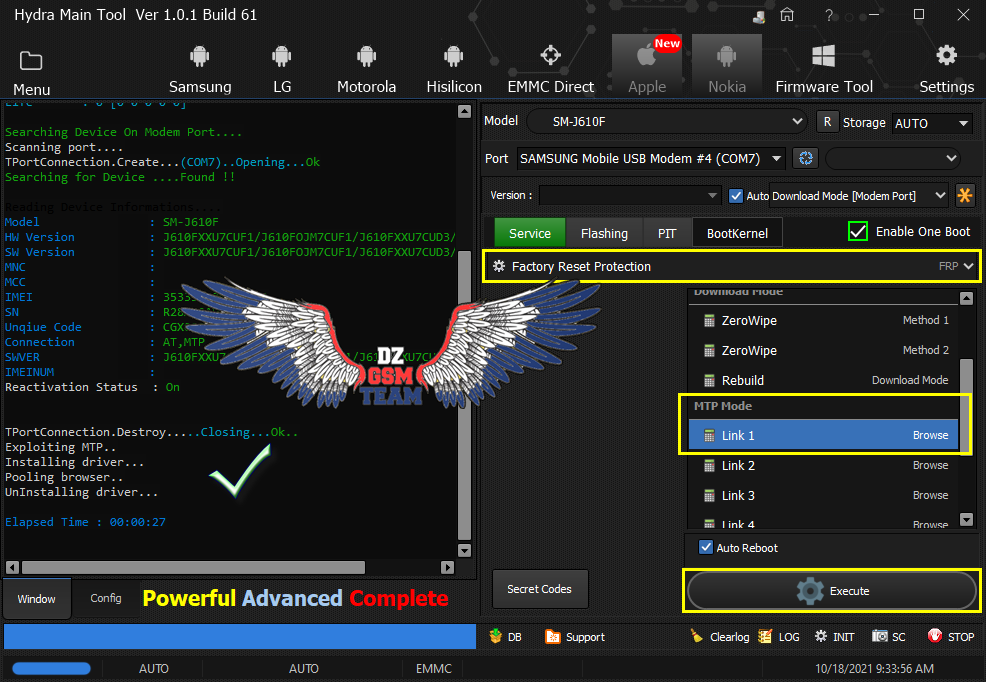
كود:
[B][FONT=Arial Black][SIZE=2]Searching Device On Modem Port....
Scanning port....
TPortConnection.Create...(COM7)..Opening...Ok
Searching for Device ....Found !!
Reading Device Informations....
Model : SM-J610F
HW Version : J610FXXU7CUF1/J610FOJM7CUF1/J610FXXU7CUD3/J610FXXU7CUF1
SW Version : J610FXXU7CUF1/J610FOJM7CUF1/J610FXXU7CUD3/J610FXXU7CUF1
MNC :
MCC :
IMEI : 35XXXXXXXXXXXX
SN : XXXXXXXX
Unqiue Code : CGX00056C9B2A36
Connection : AT,MTP
SWVER : J610FXXU7CUF1/J610FOJM7CUF1/J610FXXU7CUD3/J610FXXU7CUF1
IMEINUM :
Reactivation Status : On
TPortConnection.Destroy.....Closing...Ok..
Exploiting MTP..
Installing driver...
Pooling browser..
UnInstalling driver...
Elapsed Time : 00:00:27
[/SIZE][/FONT][/B][video=youtube;hRqU6lFb-8U]https://www.youtube.com/watch?v=hRqU6lFb-8U&ab_channel=SmartPhoneRepair[/video]
Khaled bessous
عضو نشط
- إنضم
- 21 فيفري 2018
- المشاركات
- 30
- مستوى التفاعل
- 48
- النقاط
- 18
رد: تجارب الأعضاء الناجحة فى تصليح و تفليش و فك شفرات الأجهزة على Hydra Dongle
السلام عليكم و رحمة الله
حذف النمط و حساب قوقل لهاتف wiko robby 2 بواسطة HYDRA TOOL
[video=youtube;L6cavs3-LGk]https://www.youtube.com/watch?v=L6cavs3-LGk&ab_channel=KhaledBessous[/video]
اللودر
https://www.mediafire.com/file/i4ve7...9_ddr.zip/file
السلام عليكم و رحمة الله
حذف النمط و حساب قوقل لهاتف wiko robby 2 بواسطة HYDRA TOOL
[video=youtube;L6cavs3-LGk]https://www.youtube.com/watch?v=L6cavs3-LGk&ab_channel=KhaledBessous[/video]
اللودر
https://www.mediafire.com/file/i4ve7...9_ddr.zip/file
رد: تجارب الأعضاء الناجحة فى تصليح و تفليش و فك شفرات الأجهزة على Hydra Dongle
OPPO A37f Read Pattern Ok
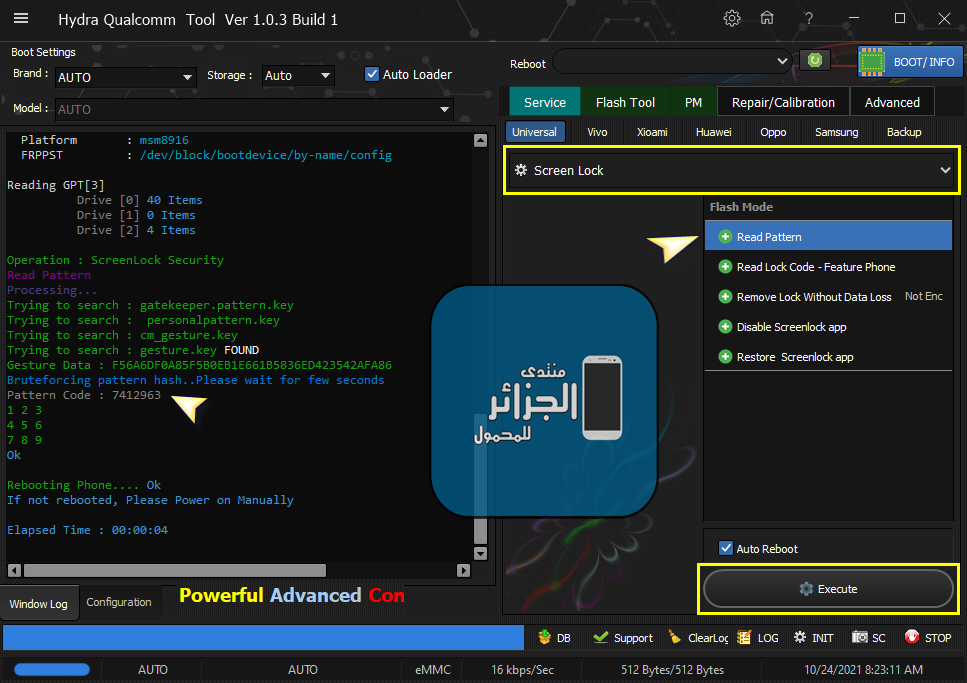
OPPO A37f Read Pattern Ok
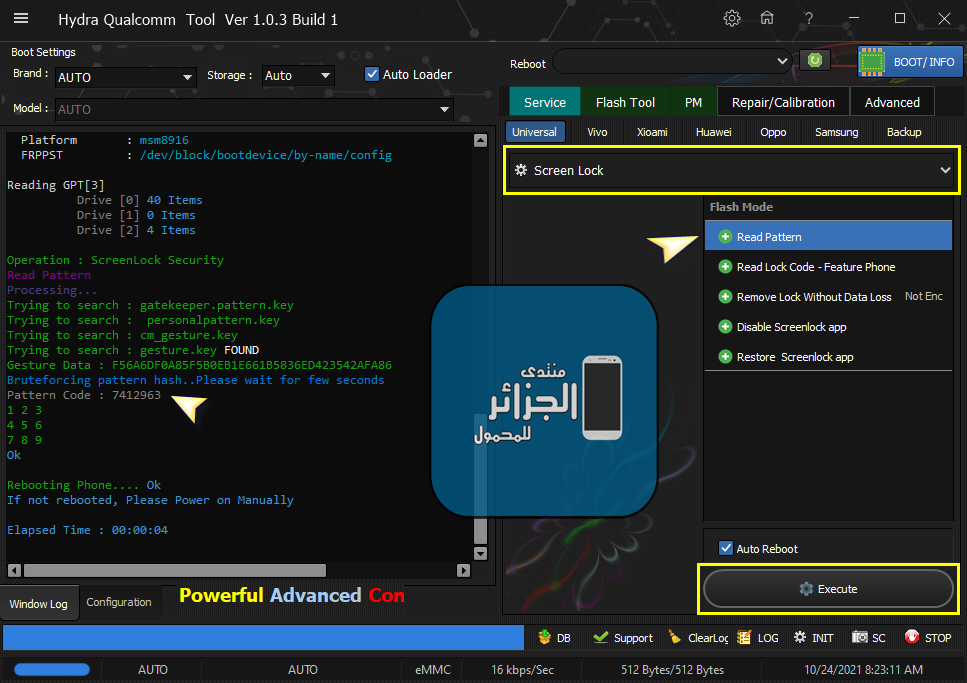
كود:
[B][FONT=Arial Black][SIZE=2]PreOperation Configuration
Brand : AUTO Model : AUTO Storage : Auto
Loader: Auto
Port : Auto
Searching for Qualcomm 9008 Device...Found
FriendlyName :Qualcomm HS-USB QDLoader 9008 (COM14)
SymbolicName :\??\USB#VID_05C6&PID_9008#6&12e3c9ed&0&1#{a5dcbf10-6530-11d2-901f-00c04fb951ed}
Driver Ver :03/21/2018,2.1.3.1
Getting device info..Ok
Device MODE : Firehose
Connecting to Firehose...
Ping.. Ok
Configuration.......
Identifying Chip....
Ok
Chip Configuration :
MemoryName : eMMC
MaxPayloadSizeToTargetInBytes : 16384
MaxPayloadSizeToTargetInBytesSupported : 16384
MaxPayloadSizeFromTargetInBytes : 4096
MaxXMLSizeInBytes : 4096
TargetName : 8916
Version : 1
Protocol : Universal
Running : Ok
Phone Information.....
Brand : OPPO
Vendor : OPPO
Model : A37f
ID : LMY47V
SDK : 22
Release : 5.1.1
ABI : arm64-v8a
CPU abilist : arm64-v8a,armeabi-v7a,armeabi
Description : msm8916_64-user 5.1.1 LMY47V eng.root.20171008.172519 release-keys
Board : msm8916
Display ID : A37fEX_11_171008
Security Patch : 2017-09-01
Platform : msm8916
FRPPST : /dev/block/bootdevice/by-name/config
Reading GPT[3]
Drive [0] 40 Items
Drive [1] 0 Items
Drive [2] 4 Items
[COLOR="#FF0000"]Operation : ScreenLock Security
Read Pattern
[/COLOR]Processing...
Trying to search : gatekeeper.pattern.key
Trying to search : personalpattern.key
Trying to search : cm_gesture.key
Trying to search : gesture.key FOUND
Gesture Data : F56A6DF0A85F5B0EB1E661B5836ED423542AFA86
Bruteforcing pattern hash..Please wait for few seconds
[COLOR="#008000"]Pattern Code : 7412963
[/COLOR]1 2 3
4 5 6
7 8 9
[COLOR="#008000"]Ok[/COLOR]
Rebooting Phone.... Ok
If not rebooted, Please Power on Manually
Elapsed Time : 00:00:04
[/SIZE][/FONT][/B]رد: تجارب الأعضاء الناجحة فى تصليح و تفليش و فك شفرات الأجهزة على Hydra Dongle
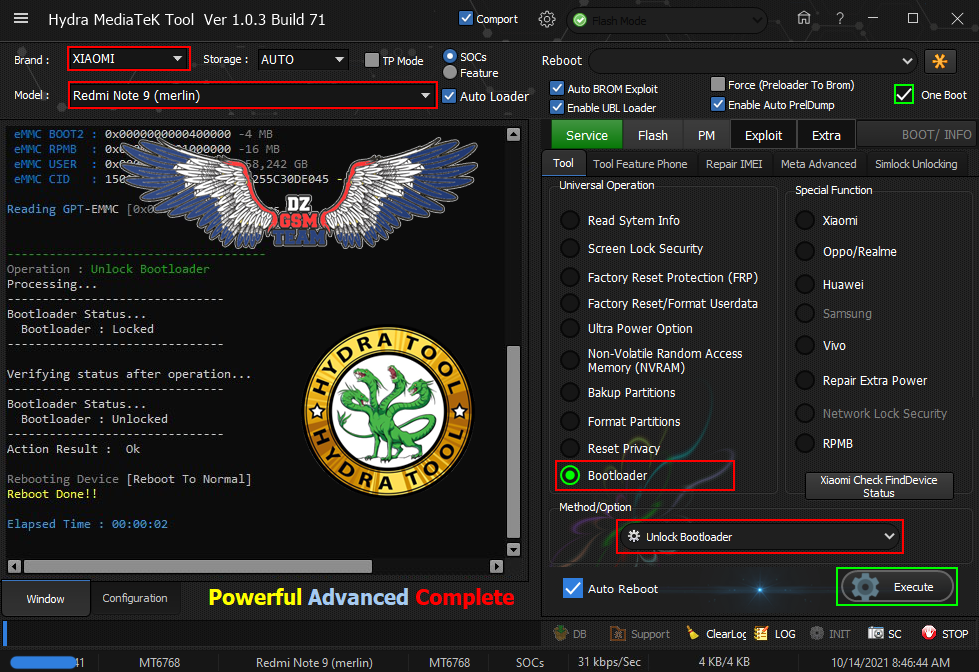
Redmi 9C NFC (angelican) Unlock Bootloader Done
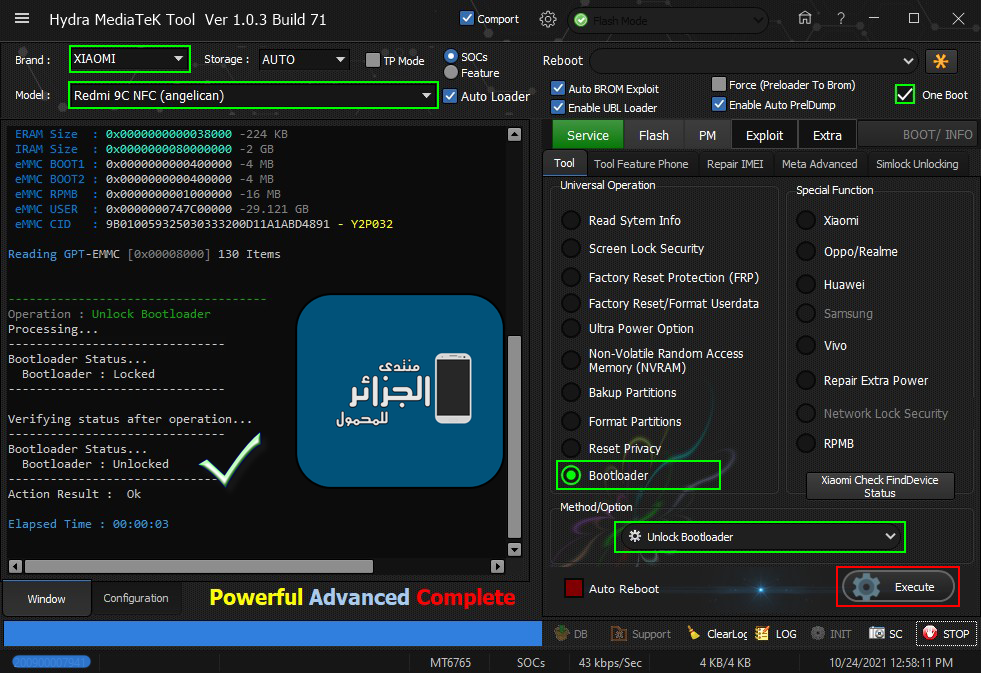

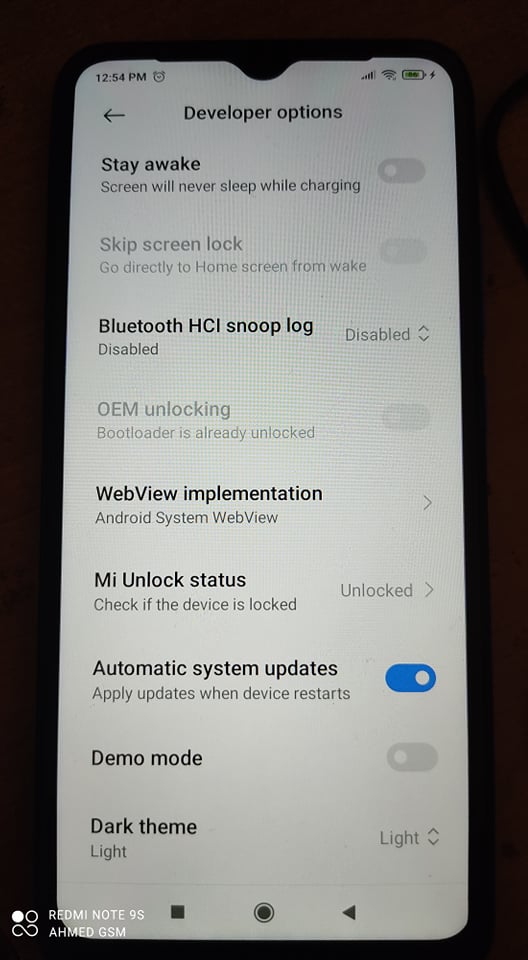
Redmi 9C NFC (angelican) Unlock Bootloader Done
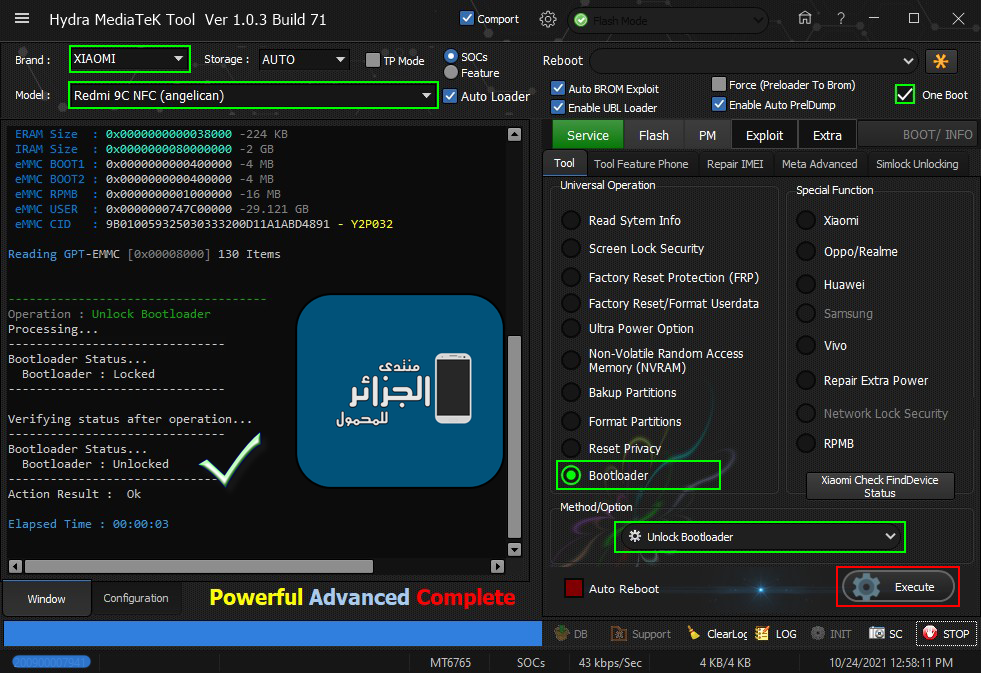
كود:
[B][FONT=Arial Black][SIZE=2]Searching for MTK Device...Found
Port Identification :Flashmode BROM
FriendlyName :MediaTek USB Port_V1633 (COM21)
Device :6&12e3c9ed&0&1
SymbolicName :\??\USB#VID_0E8D&PID_0003#6&12e3c9ed&0&1#{a5dcbf10-6530-11d2-901f-00c04fb951ed}
Driver Ver :01/22/2015,3.0.1504.0
Opened handle..
Reading Device UniqueID, RAM and Flash Chip Info...
UNIQUE ID : 9D8775412A913D705FA216AA5E3195DD
ERAM Size : 0x0000000000038000 -224 KB
IRAM Size : 0x0000000080000000 -2 GB
eMMC BOOT1 : 0x0000000000400000 -4 MB
eMMC BOOT2 : 0x0000000000400000 -4 MB
eMMC RPMB : 0x0000000001000000 -16 MB
eMMC USER : 0x0000000747C00000 -29.121 GB
eMMC CID : 9B010059325030333200D11A1ABD4891 - Y2P032
Reading GPT-EMMC [0x00008000] 130 Items
-------------------------------------
Operation : [COLOR="#FF8C00"]Unlock Bootloader[/COLOR]
Processing...
-------------------------------
Bootloader Status...
Bootloader : [COLOR="#FF0000"]Locked[/COLOR]
-------------------------------
Verifying status after operation...
-------------------------------
Bootloader Status...
Bootloader : [COLOR="#008000"]Unlocked[/COLOR]
-------------------------------
Action Result : [COLOR="#008000"]Ok[/COLOR]
Elapsed Time : 00:00:03
[/SIZE][/FONT][/B]
رد: تجارب الأعضاء الناجحة فى تصليح و تفليش و فك شفرات الأجهزة على Hydra Dongle
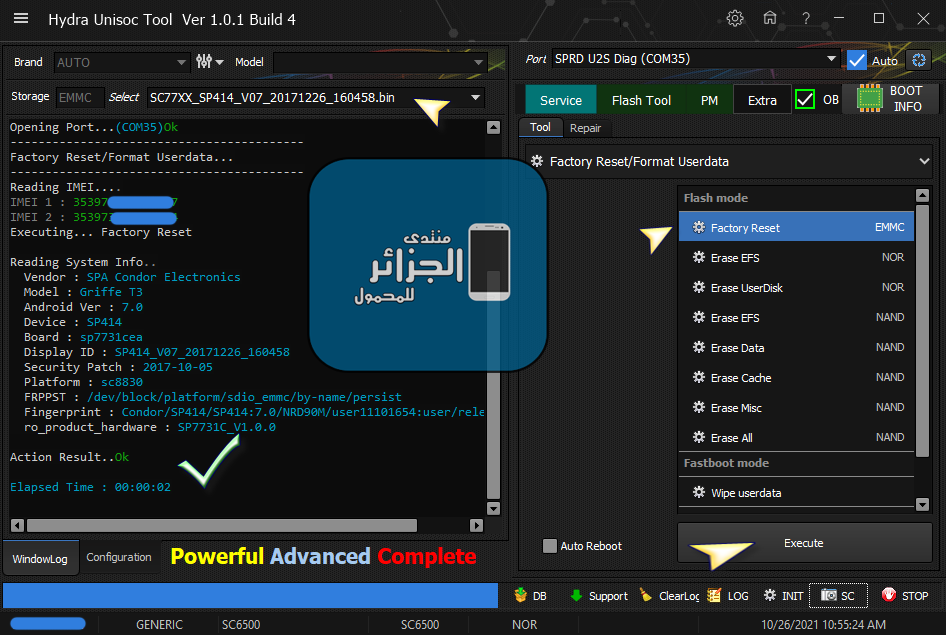
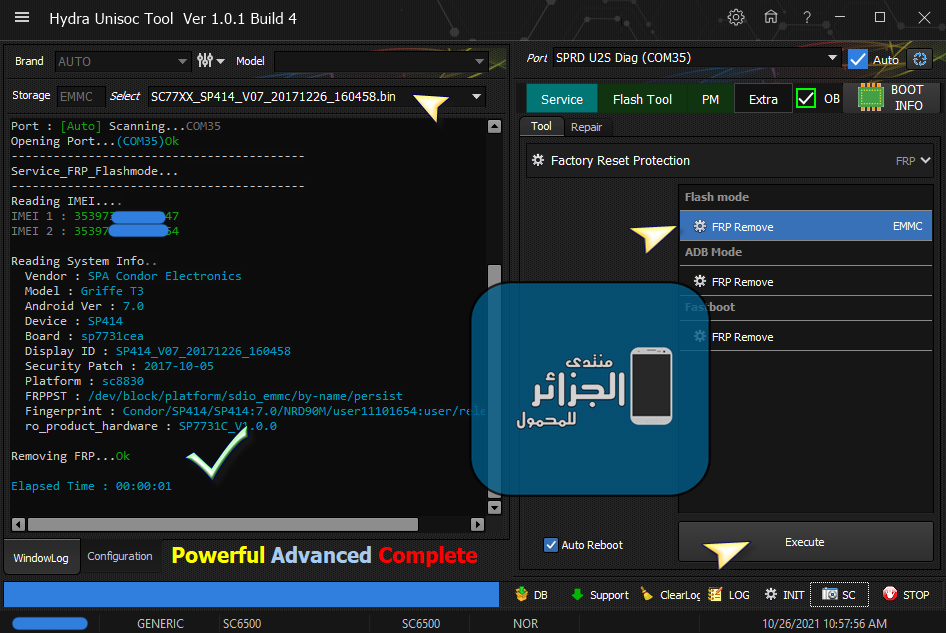
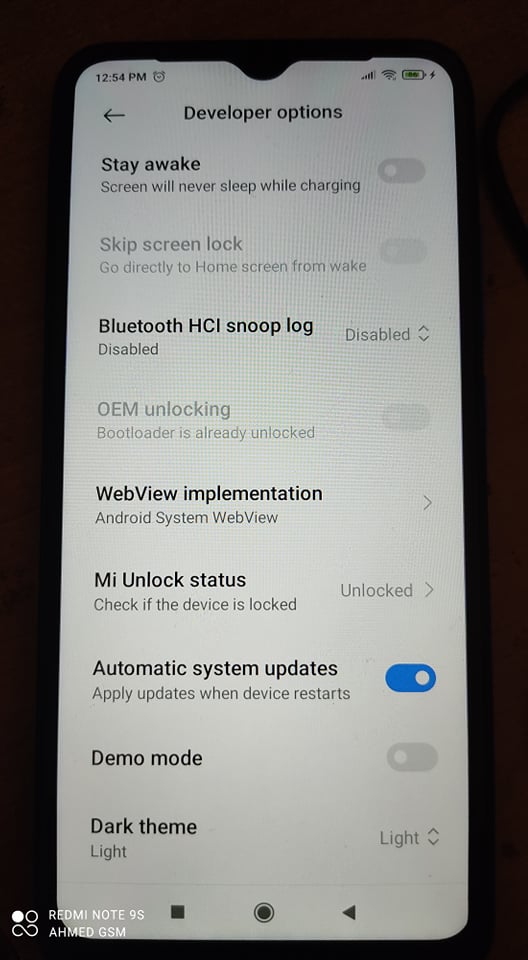
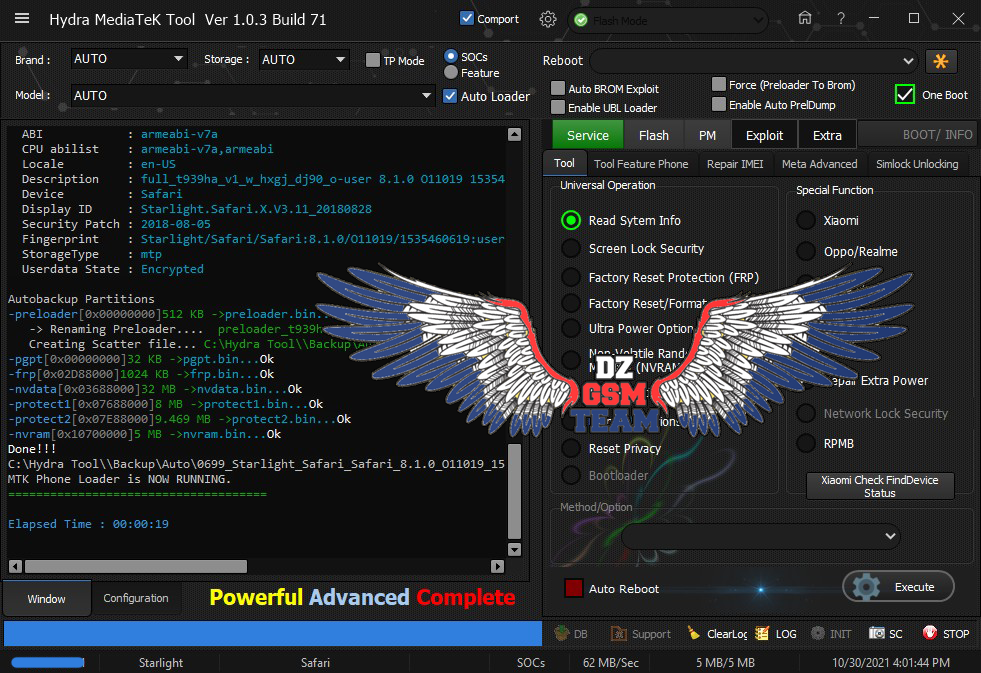
Starlight Safari (Safeformat + ZeroWipe FRP) Done
Hydra MTK Tool
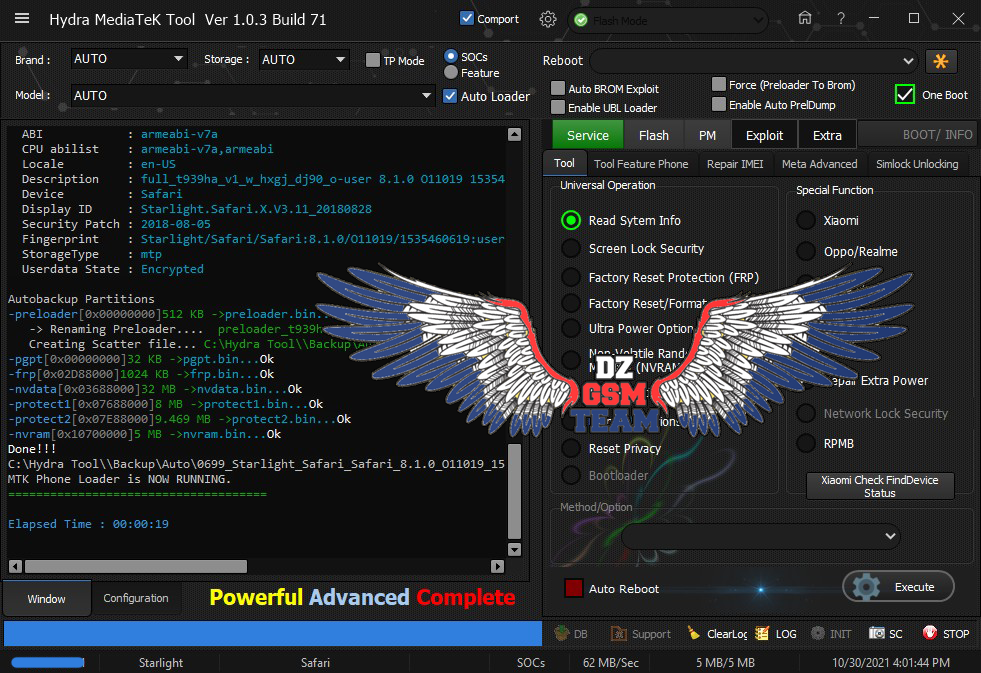
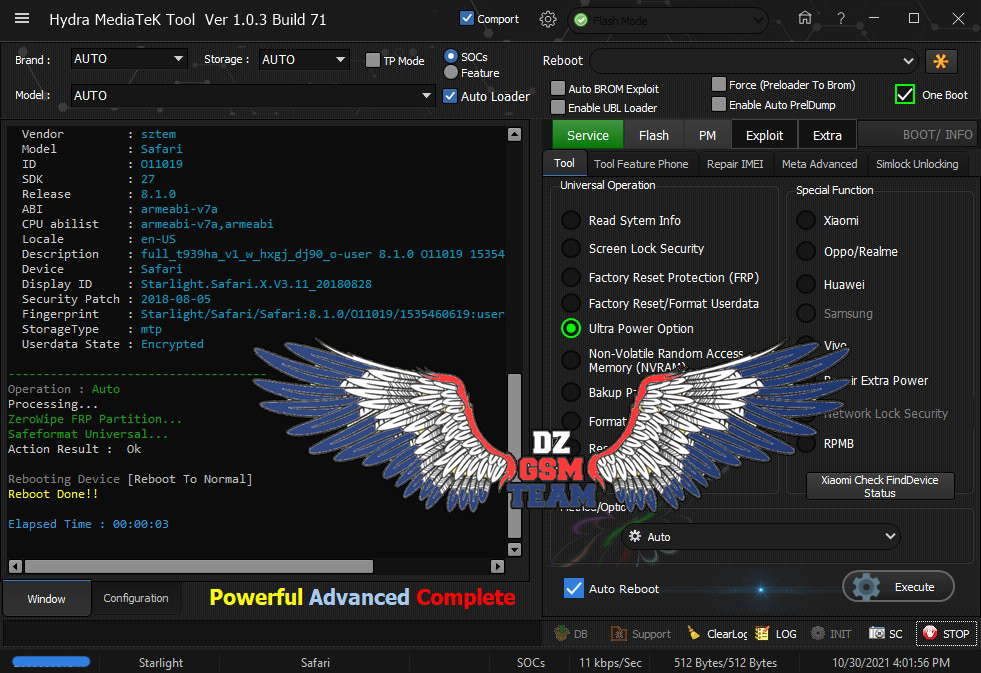
Starlight Safari (Safeformat + ZeroWipe FRP) Done
Hydra MTK Tool
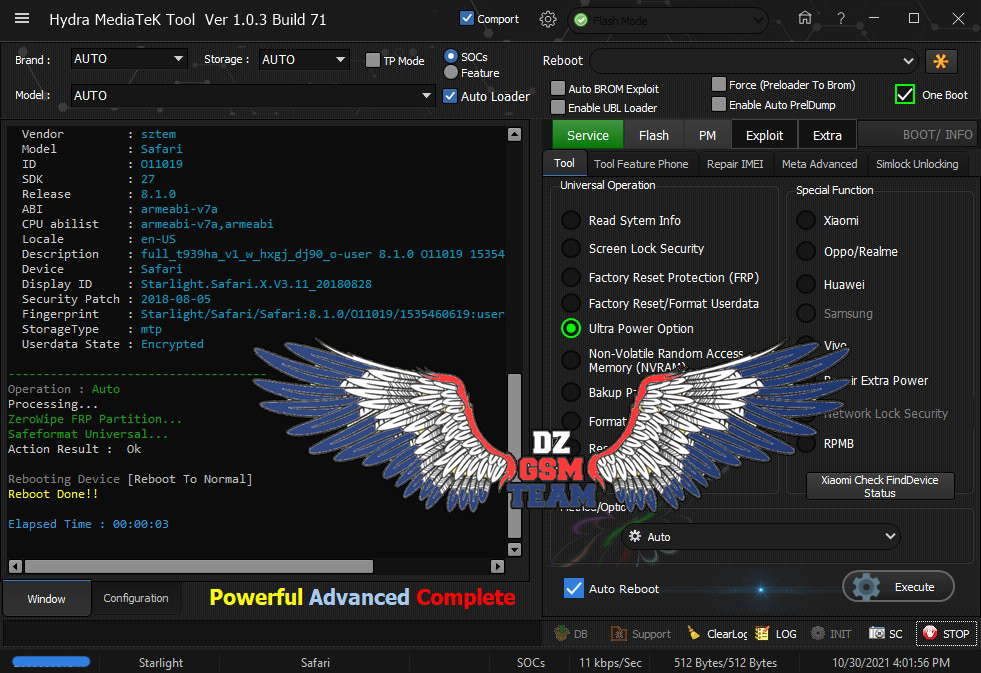
كود:
[B][FONT=Arial Black][SIZE=2]Searching for MTK Device...Found
Port Identification :Flashmode Preloader
FriendlyName :MediaTek PreLoader USB VCOM_V1633 (Android) (COM3)
Device :6&12e3c9ed&0&1
SymbolicName :\??\USB#VID_0E8D&PID_2000#6&12e3c9ed&0&1#{a5dcbf10-6530-11d2-901f-00c04fb951ed}
Driver Ver :01/22/2015,3.0.1504.0
Opened handle..
Reading Device UniqueID, RAM and Flash Chip Info...
UNIQUE ID : 2B1DB34FE59E92D1467FBD70EC54612B
ERAM Size : 0x0000000000020000 -128 KB
IRAM Size : 0x0000000080000000 -2 GB
eMMC BOOT1 : 0x0000000000400000 -4 MB
eMMC BOOT2 : 0x0000000000400000 -4 MB
eMMC RPMB : 0x0000000000400000 -4 MB
eMMC USER : 0x000000039D000000 -14.453 GB
eMMC CID : 8801034D3842313647281058692775B1 - M8B16G
Reading GPT-EMMC [0x00008000] 130 Items
Reading System Info
Brand : Starlight
Vendor : sztem
Model : Safari
ID : O11019
SDK : 27
Release : 8.1.0
ABI : armeabi-v7a
CPU abilist : armeabi-v7a,armeabi
Locale : en-US
Description : full_t939ha_v1_w_hxgj_dj90_o-user 8.1.0 O11019 1535460619 release-keys
Device : Safari
Display ID : Starlight.Safari.X.V3.11_20180828
Security Patch : 2018-08-05
Fingerprint : Starlight/Safari/Safari:8.1.0/O11019/1535460619:user/release-keys
StorageType : mtp
Userdata State : Encrypted
-------------------------------------
Operation : Auto
Processing...
ZeroWipe FRP Partition...
Safeformat Universal...
Action Result : Ok
Rebooting Device [Reboot To Normal]
Reboot Done!!
Elapsed Time : 00:00:03
[/SIZE][/FONT][/B]mounirblidaa
عضو أساسي
رد: تجارب الأعضاء الناجحة فى تصليح و تفليش و فك شفرات الأجهزة على Hydra Dongle
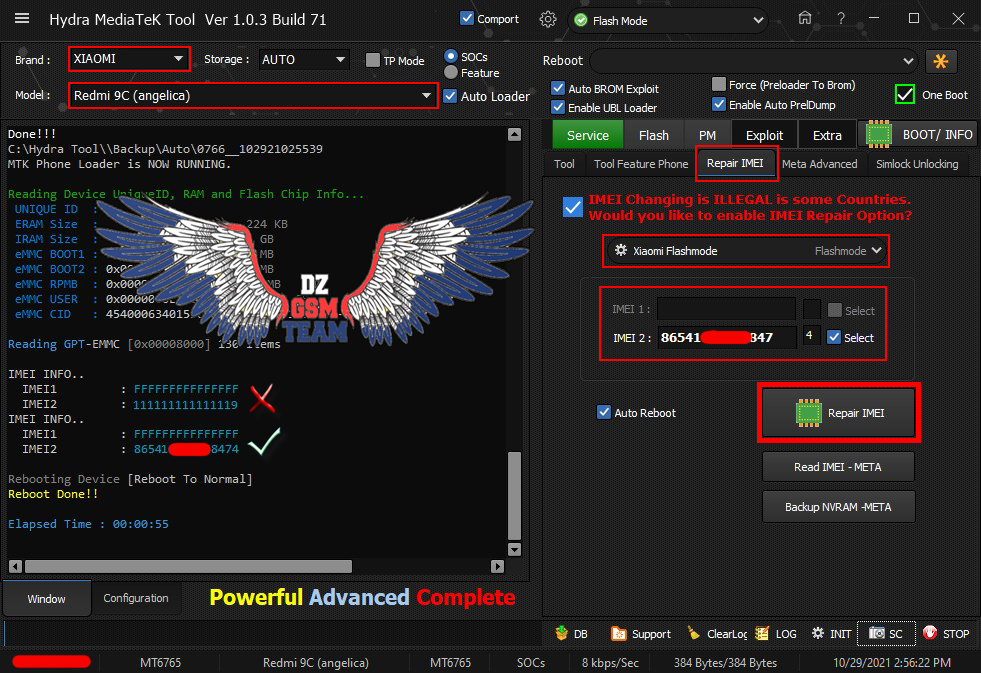
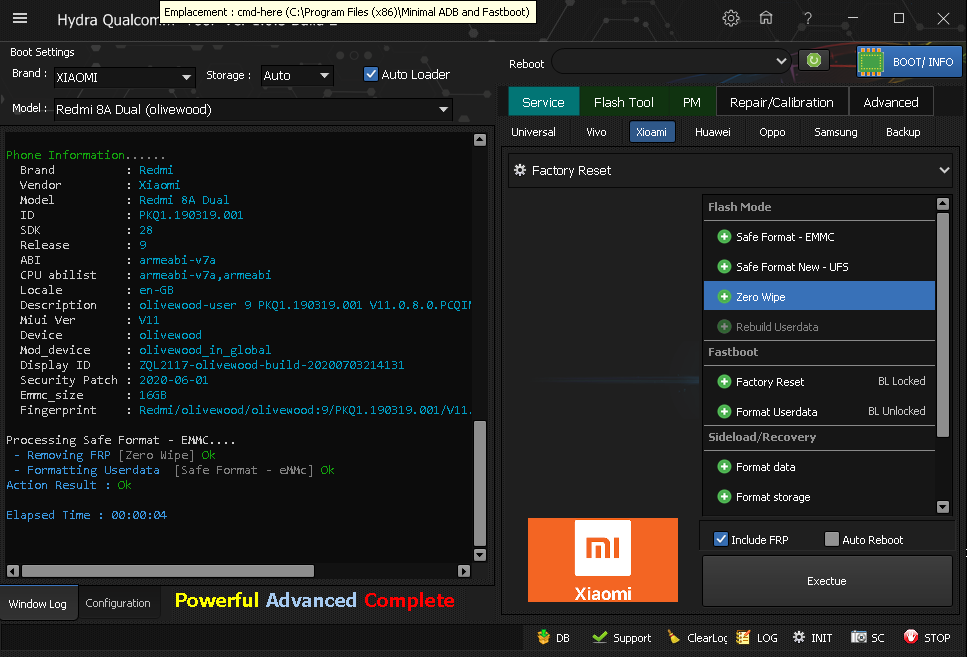
REDMI 8A FRP Remove
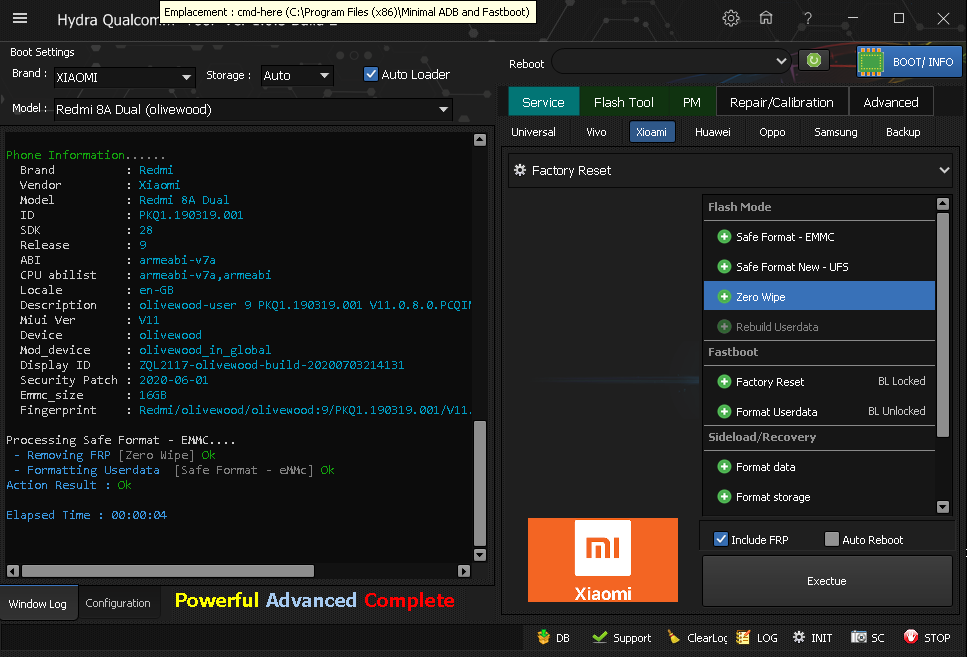
REDMI 8A FRP Remove
رد: تجارب الأعضاء الناجحة فى تصليح و تفليش و فك شفرات الأجهزة على Hydra Dongle
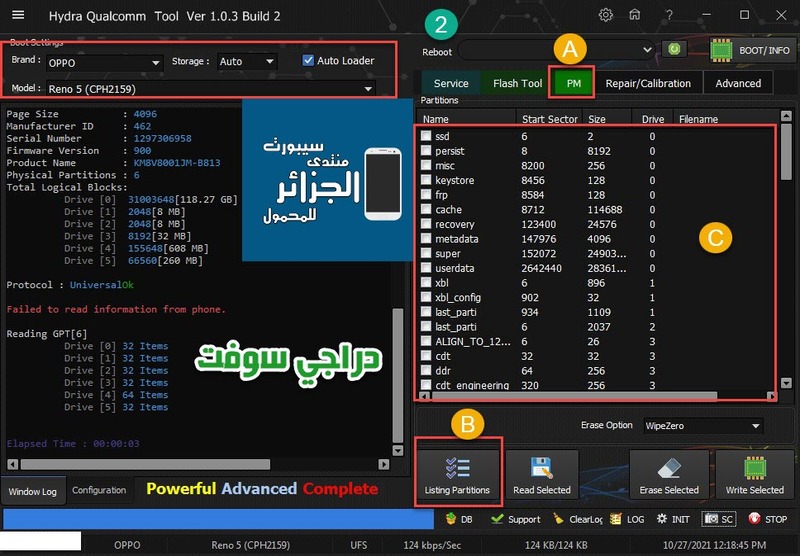
OPPO A15s (CPH2179) Remove OPPO/ID DONE
Hydra MTK Tool

OPPO A15s (CPH2179) Remove OPPO/ID DONE
Hydra MTK Tool

كود:
[B][FONT=Arial Black][SIZE=2]Searching for MTK Device...Found
Port Identification :Flashmode BROM
FriendlyName :MediaTek USB Port_V1632 (COM6)
Device :6&12e3c9ed&0&1
SymbolicName :\??\USB#VID_0E8D&PID_0003#5&64eeb62&0&2#{a5dcbf10-6530-11d2-901f-00c04fb951ed}
Driver Ver :01/22/2016,3.2
Opened handle..
Reading Device UniqueID, RAM and Flash Chip Info...
UNIQUE ID : FC42BCED8C6608F964412DD64F22EC4D
ERAM Size : 0x0000000000038000 -224 KB
IRAM Size : 0x00000000C0000000 -3 GB
eMMC BOOT1 : 0x0000000000400000 -4 MB
eMMC BOOT2 : 0x0000000000400000 -4 MB
eMMC RPMB : 0x0000000001000000 -16 MB
eMMC USER : 0x0000000747C00000 -29.121 GB
eMMC CID : 150407865412F84442E2C2210B2C36D3 - DX68NB
Reading GPT -EMMC [0x00008000] 130 Items
-------------------------------------
Operation : [COLOR="#008000"]Remove Oppo/Realme ID[/COLOR]
Processing...
ACK : 0xFFFF0000[]
[COLOR="#008000"]Done
Action Result : Ok[/COLOR]
Elapsed Time : 00:00:01
[/SIZE][/FONT][/B]رد: تجارب الأعضاء الناجحة فى تصليح و تفليش و فك شفرات الأجهزة على Hydra Dongle
Samsung Galaxy M11 (SM-M115F) Removing FRP ADB Mode
Hydra Main Tool
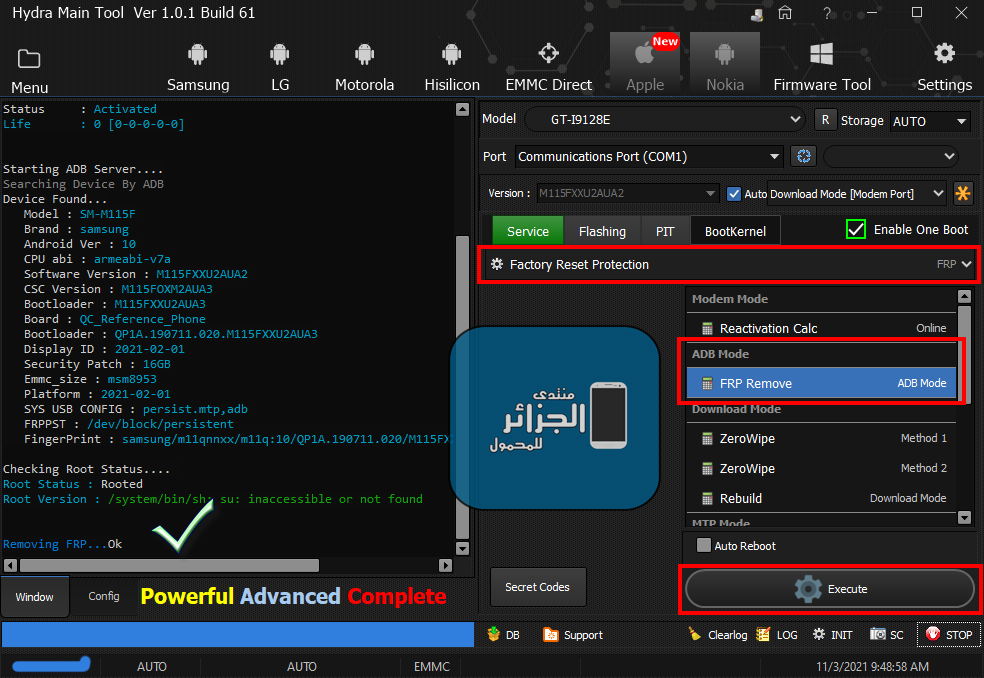
Samsung Galaxy M11 (SM-M115F) Removing FRP ADB Mode
Hydra Main Tool
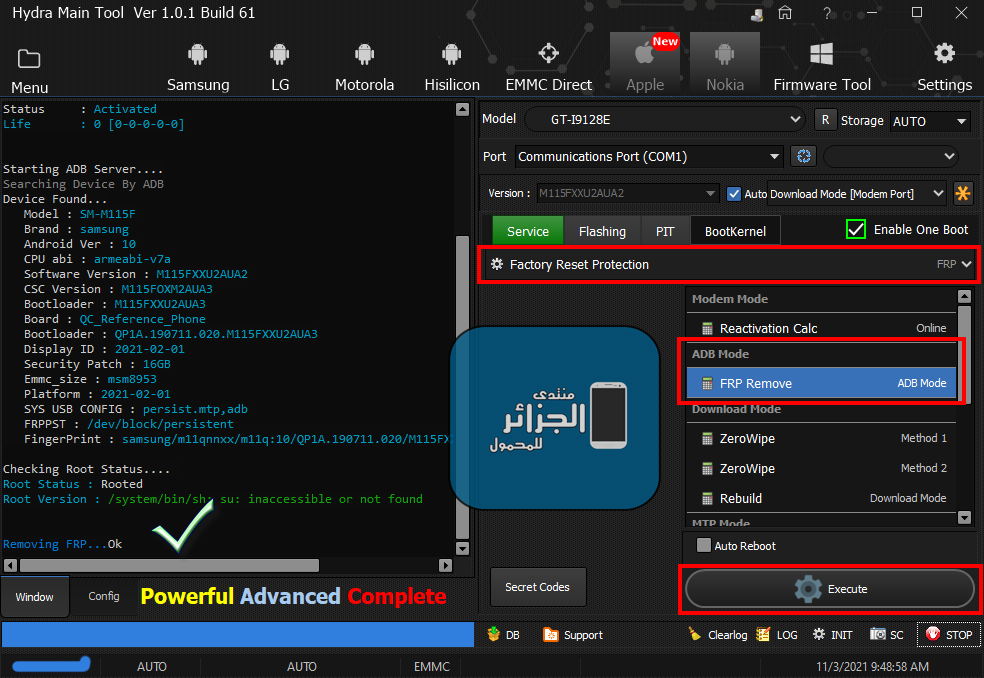
كود:
[B][FONT=Arial Black][SIZE=2]Starting ADB Server....
Searching Device By ADB
Device Found...
Model : SM-M115F
Brand : samsung
Android Ver : 10
CPU abi : armeabi-v7a
Software Version : M115FXXU2AUA2
CSC Version : M115FOXM2AUA3
Bootloader : M115FXXU2AUA3
Board : QC_Reference_Phone
Bootloader : QP1A.190711.020.M115FXXU2AUA3
Display ID : 2021-02-01
Security Patch : 16GB
Emmc_size : msm8953
Platform : 2021-02-01
SYS USB CONFIG : persist.mtp,adb
FRPPST : /dev/block/persistent
FingerPrint : samsung/m11qnnxx/m11q:10/QP1A.190711.020/M115FXXU2AUA3:user/release-keys
Checking Root Status....
Root Status : Rooted
Root Version : /system/bin/sh: su: inaccessible or not found
Removing FRP...Ok
[/SIZE][/FONT][/B]رد: تجارب الأعضاء الناجحة فى تصليح و تفليش و فك شفرات الأجهزة على Hydra Dongle
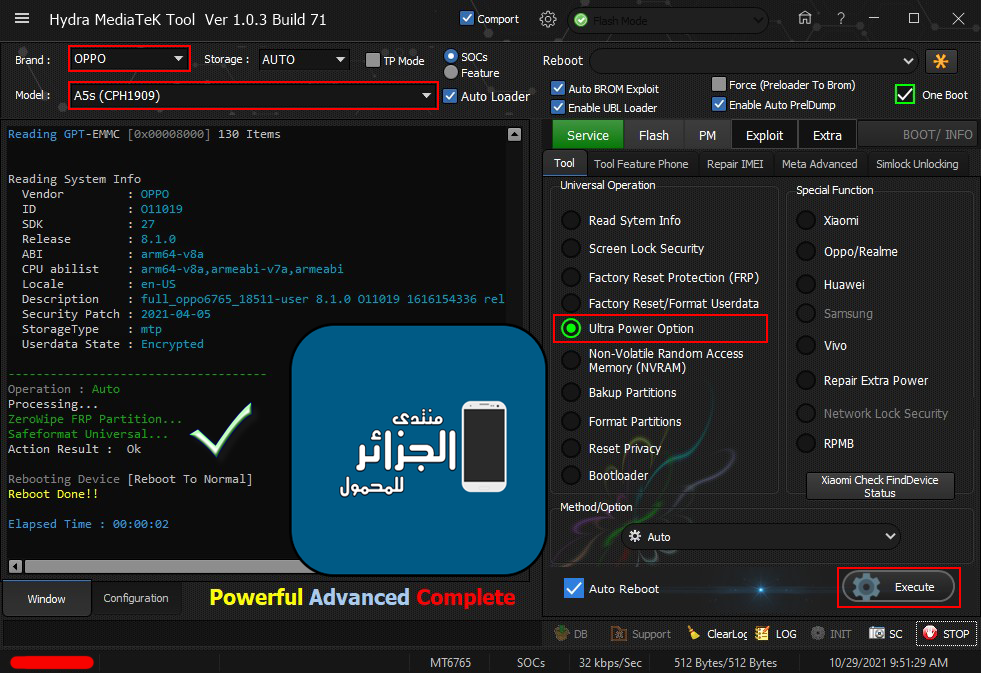
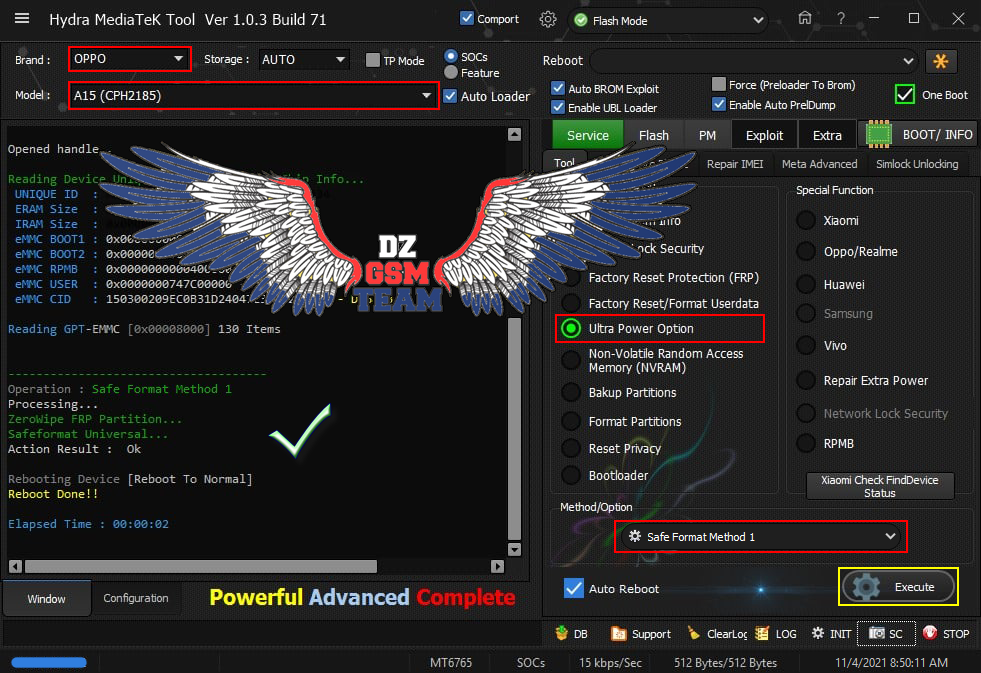
OPPO A15 (CPH2185) Ultra Power Option
Safe Format Method 1 + Zirowipe FRP
Hydra MTK Tool - ONE CLICK
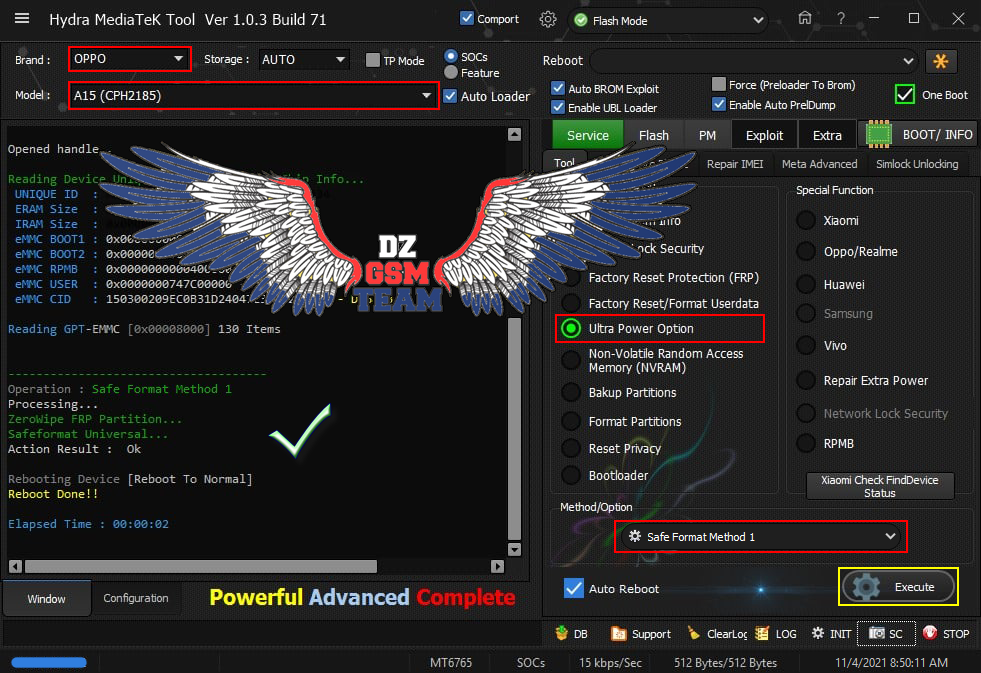
OPPO A15 (CPH2185) Ultra Power Option
Safe Format Method 1 + Zirowipe FRP
Hydra MTK Tool - ONE CLICK
رد: تجارب الأعضاء الناجحة فى تصليح و تفليش و فك شفرات الأجهزة على Hydra Dongle
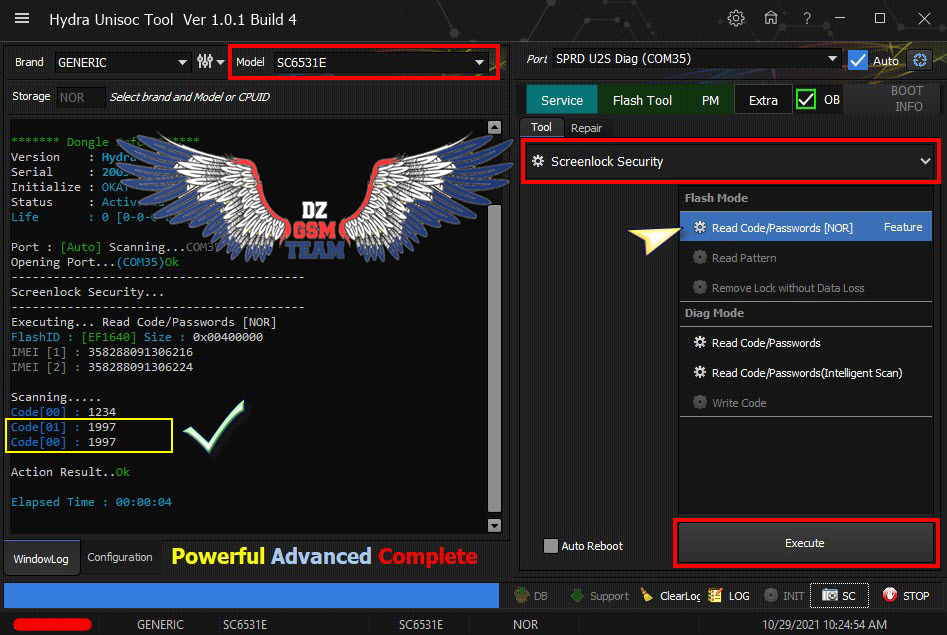
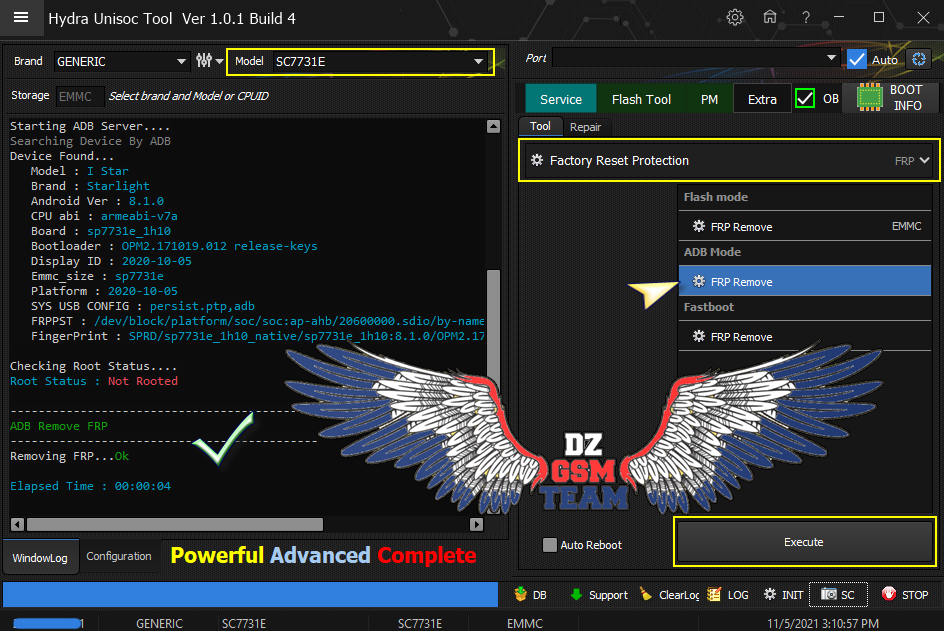
Starlight I Star (sp7731e) Remove FRP ADB Done
Hydra Unisoc Tool
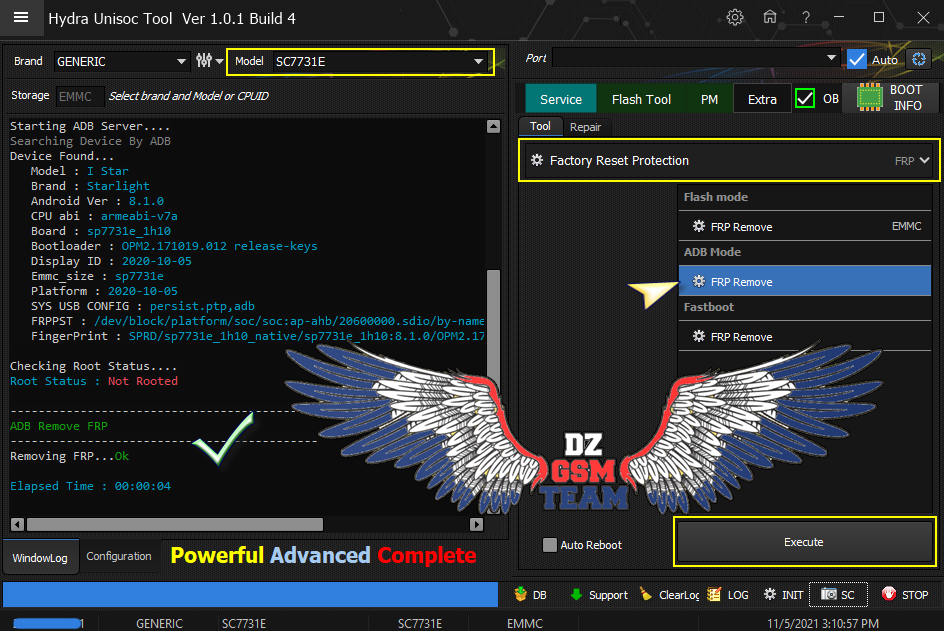
Starlight I Star (sp7731e) Remove FRP ADB Done
Hydra Unisoc Tool
كود:
[B][FONT=Arial Black][SIZE=2]Starting ADB Server....
Searching Device By ADB
Device Found...
Model : I Star
Brand : Starlight
Android Ver : 8.1.0
CPU abi : armeabi-v7a
Board : sp7731e_1h10
Bootloader : OPM2.171019.012 release-keys
Display ID : 2020-10-05
Emmc_size : sp7731e
Platform : 2020-10-05
SYS USB CONFIG : persist.ptp,adb
FRPPST : /dev/block/platform/soc/soc:ap-ahb/20600000.sdio/by-name/persist
FingerPrint : SPRD/sp7731e_1h10_native/sp7731e_1h10:8.1.0/OPM2.171019.012/17217:user/release-keys
Checking Root Status....
Root Status : Not Rooted
--------------------------------------------
[COLOR="#008000"]ADB Remove FRP
[/COLOR]--------------------------------------------
Removing FRP...[COLOR="#008000"]Ok[/COLOR]
Elapsed Time : 00:00:04
[/SIZE][/FONT][/B]