تثبيت التطبيق
How to install the app on iOS
Follow along with the video below to see how to install our site as a web app on your home screen.
ملاحظة: This feature may not be available in some browsers.
أنت تستخدم أحد المتصفحات القديمة. قد لا يتم عرض هذا الموقع أو المواقع الأخرى بشكل صحيح.
يجب عليك ترقية متصفحك أو استخدام أحد المتصفحات البديلة.
يجب عليك ترقية متصفحك أو استخدام أحد المتصفحات البديلة.
تجارب الاعضاء فى تفليش وعمل ريبير وفك الشفرة على NckBox
- إنضم
- 16 سبتمبر 2012
- المشاركات
- 3,612
- مستوى التفاعل
- 3,310
- النقاط
- 113
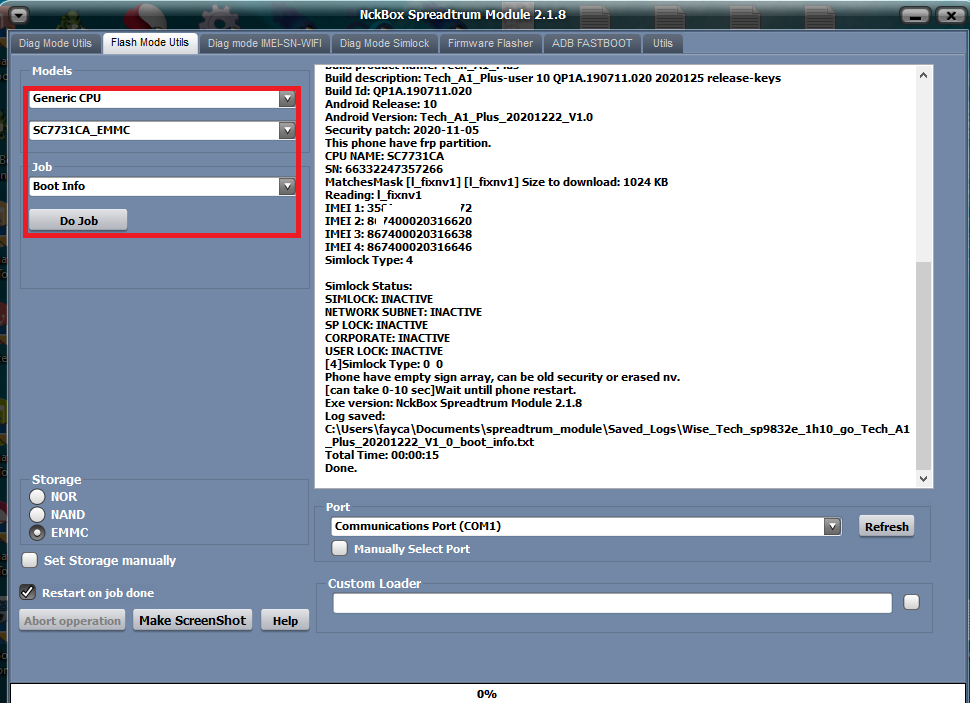
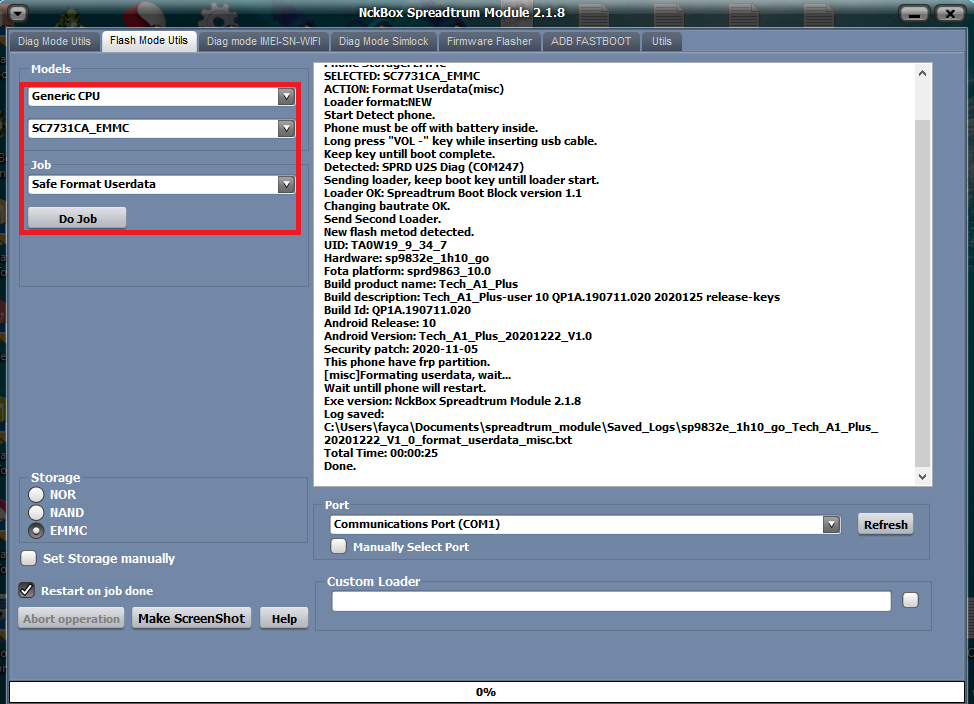
Wise Tech (Tech A1 Plus) Userdata Reset
Wise Tech (Tech A1 Plus) Userdata Reset
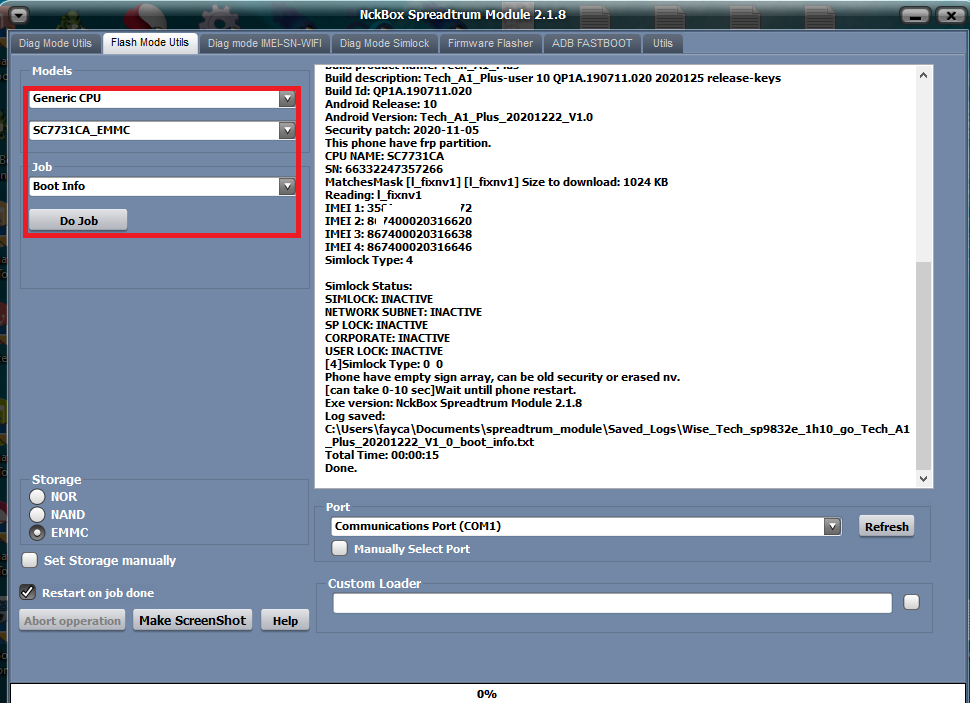
كود:
Phone Storage: EMMCSELECTED: SC7731CA_EMMC
ACTION: Format Userdata(misc)
Loader format:NEW
Start Detect phone.
Phone must be off with battery inside.
Long press "VOL -" key while inserting usb cable.
Keep key untill boot complete.
Detected: SPRD U2S Diag (COM247)
Sending loader, keep boot key untill loader start.
Loader OK: Spreadtrum Boot Block version 1.1
Changing bautrate OK.
Send Second Loader.
New flash metod detected.
UID: TA0W19_9_34_7
Hardware: sp9832e_1h10_go
Fota platform: sprd9863_10.0
Build product name: Tech_A1_Plus
Build description: Tech_A1_Plus-user 10 QP1A.190711.020 2020125 release-keys
Build Id: QP1A.190711.020
Android Release: 10
Android Version: Tech_A1_Plus_20201222_V1.0
Security patch: 2020-11-05
This phone have frp partition.
[misc]Formating userdata, wait...
Wait untill phone will restart.
Exe version: NckBox Spreadtrum Module 2.1.8
Log saved:
C:\Users\fayca\Documents\spreadtrum_module\Saved_Logs\sp9832e_1h10_go_Tech_A1_Plus_20201222_V1_0_format_userdata_misc.txt
Total Time: 00:00:25
Done.- إنضم
- 16 سبتمبر 2012
- المشاركات
- 3,612
- مستوى التفاعل
- 3,310
- النقاط
- 113
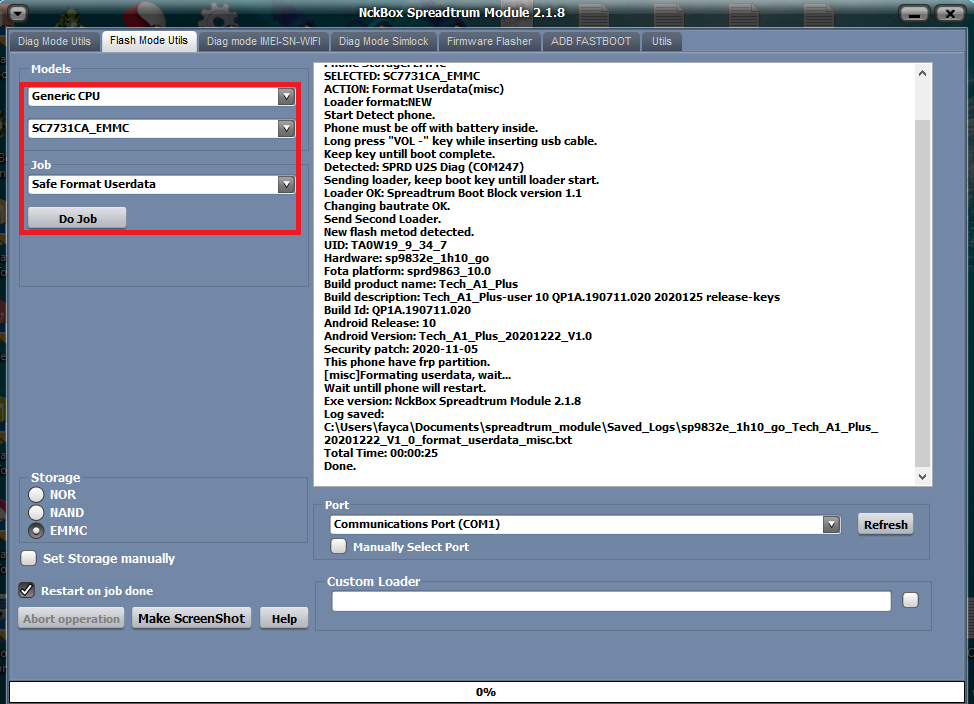
TECNO POP 2F (B1G) Reset Userdata and Remove FRP
TECNO POP 2F (B1G) Reset Userdata and Remove FRP
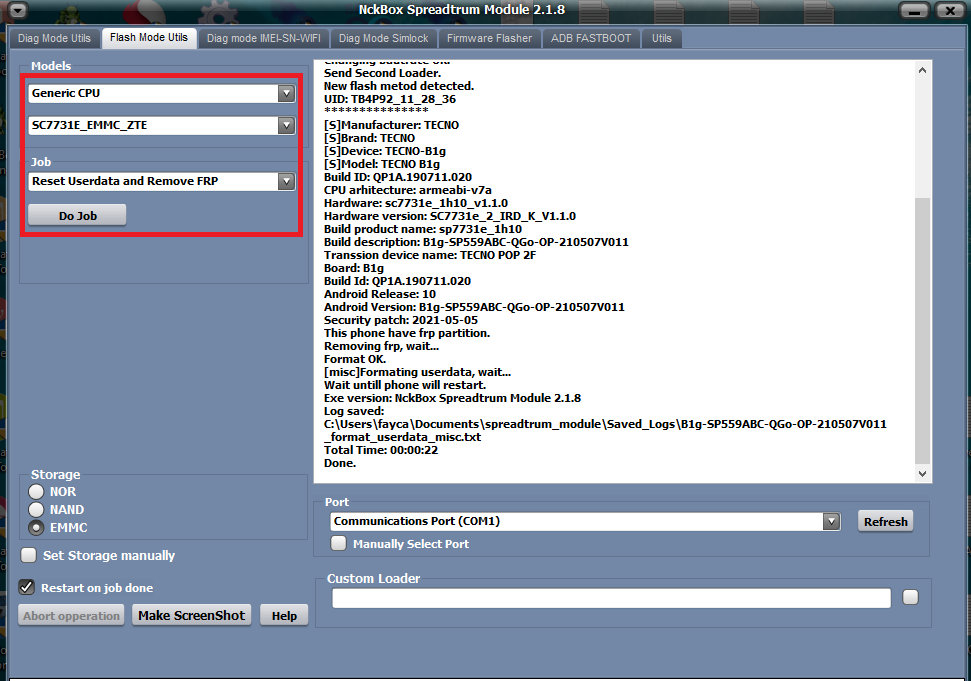
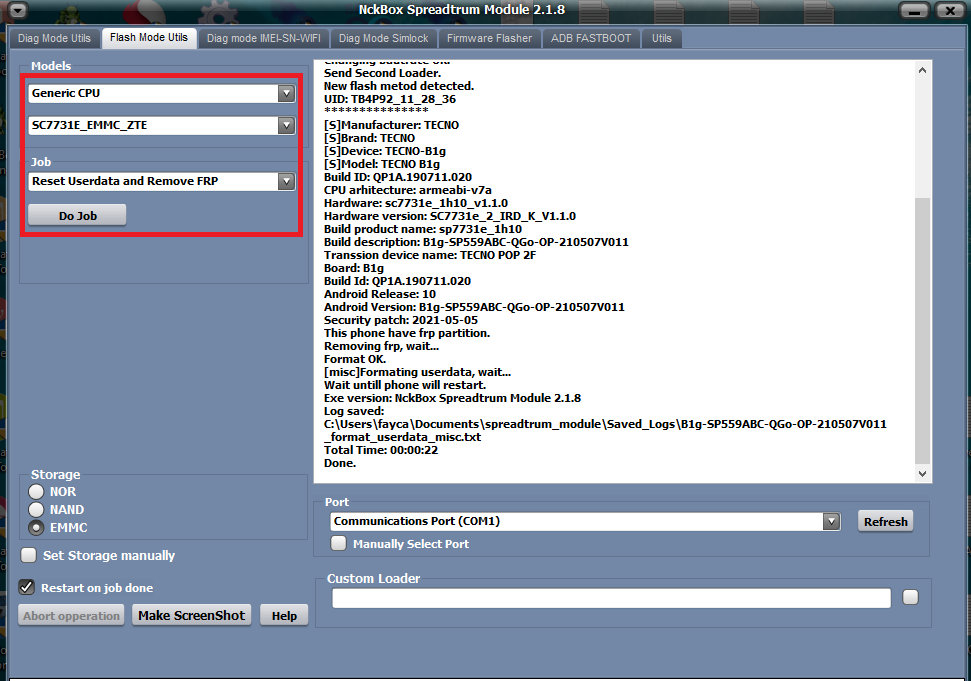
كود:
Phone Storage: EMMCSELECTED: SC7731E_EMMC_ZTE
ACTION: Reset Userdata and Remove FRP
Loader format:NEW
Start Detect phone.
Phone must be off with battery inside.
Long press "VOL -" key while inserting usb cable.
Keep key untill boot complete.
Detected: SPRD U2S Diag (COM247)
Sending loader, keep boot key untill loader start.
Loader OK: Spreadtrum Boot Block version 1.1
Changing bautrate OK.
Send Second Loader.
New flash metod detected.
UID: TB4P92_11_28_36
***************
[S]Manufacturer: TECNO
[S]Brand: TECNO
[S]Device: TECNO-B1g
[S]Model: TECNO B1g
Build ID: QP1A.190711.020
CPU arhitecture: armeabi-v7a
Hardware: sc7731e_1h10_v1.1.0
Hardware version: SC7731e_2_IRD_K_V1.1.0
Build product name: sp7731e_1h10
Build description: B1g-SP559ABC-QGo-OP-210507V011
Transsion device name: TECNO POP 2F
Board: B1g
Build Id: QP1A.190711.020
Android Release: 10
Android Version: B1g-SP559ABC-QGo-OP-210507V011
Security patch: 2021-05-05
This phone have frp partition.
Removing frp, wait...
Format OK.
[misc]Formating userdata, wait...
Wait untill phone will restart.
Exe version: NckBox Spreadtrum Module 2.1.8
Log saved:
C:\Users\fayca\Documents\spreadtrum_module\Saved_Logs\B1g-SP559ABC-QGo-OP-210507V011_format_userdata_misc.txt
Total Time: 00:00:22
Done.- إنضم
- 16 سبتمبر 2012
- المشاركات
- 3,612
- مستوى التفاعل
- 3,310
- النقاط
- 113
Condor L3 PLUS (SP637) FRP Reset
Condor L3 PLUS (SP637) FRP Reset
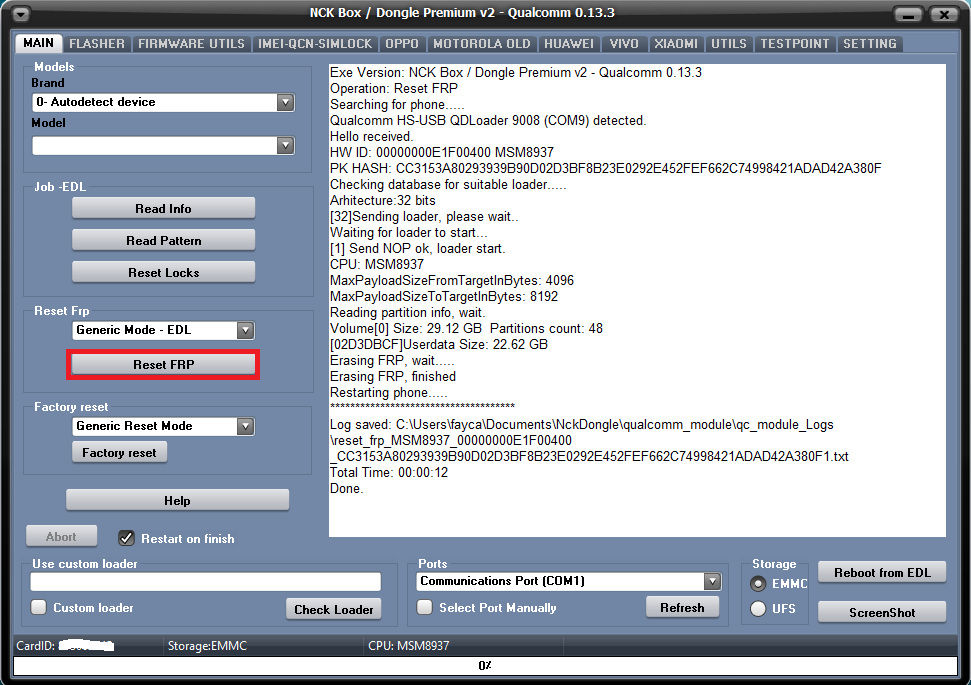
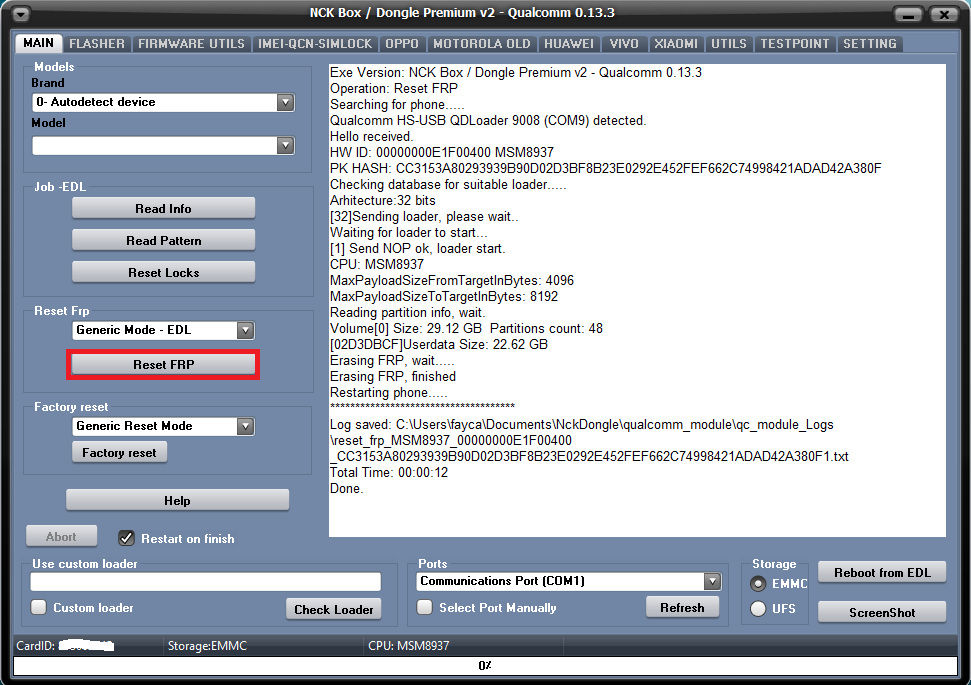
كود:
Exe Version: NCK Box / Dongle Premium v2 - Qualcomm 0.13.3Operation: Reset FRP
Searching for phone.....
Qualcomm HS-USB QDLoader 9008 (COM9) detected.
Hello received.
HW ID: 00000000E1F00400 MSM8937
PK HASH: CC3153A80293939B90D02D3BF8B23E0292E452FEF662C74998421ADAD42A380F
Checking database for suitable loader.....
Arhitecture:32 bits
[32]Sending loader, please wait..
Waiting for loader to start...
[1] Send NOP ok, loader start.
CPU: MSM8937
MaxPayloadSizeFromTargetInBytes: 4096
MaxPayloadSizeToTargetInBytes: 8192
Reading partition info, wait.
Volume[0] Size: 29.12 GB Partitions count: 48
[02D3DBCF]Userdata Size: 22.62 GB
Erasing FRP, wait.....
Erasing FRP, finished
Restarting phone.....
*************************************
Log saved: C:\Users\fayca\Documents\NckDongle\qualcomm_module\qc_module_Logs\reset_frp_MSM8937_00000000E1F00400_CC3153A80293939B90D02D3BF8B23E0292E452FEF662C74998421ADAD42A380F1.txt
Total Time: 00:00:12
Done.- إنضم
- 16 سبتمبر 2012
- المشاركات
- 3,612
- مستوى التفاعل
- 3,310
- النقاط
- 113
ACE Buzz 1 FRP Reset
ACE Buzz 1 FRP Reset
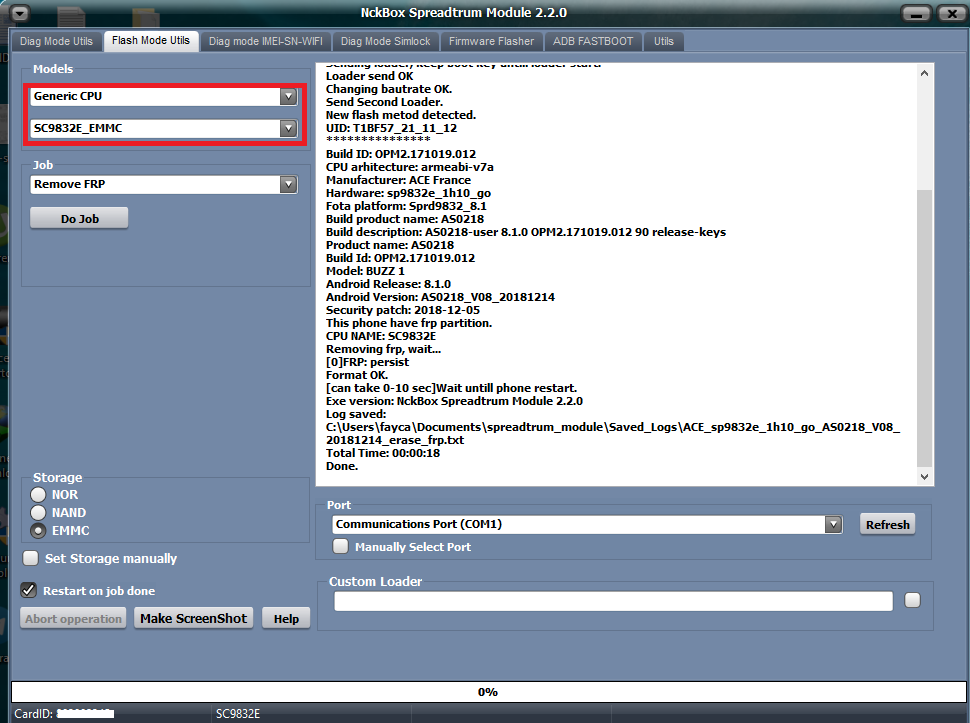
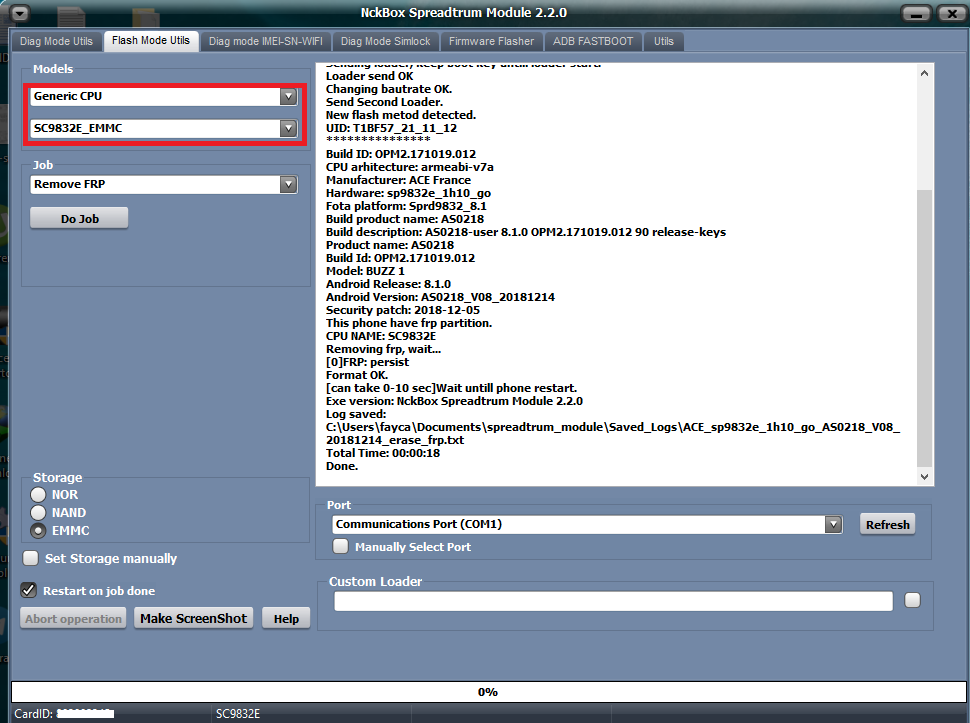
كود:
Phone Storage: EMMCSELECTED: SC9832E_EMMC
ACTION: Erase FRP
Loader format:NEW
Start Detect phone.
Phone must be off with battery inside.
Long press "VOL -" key while inserting usb cable.
Keep key untill boot complete.
Detected: SPRD U2S Diag (COM20)
Sending loader, keep boot key untill loader start.
Loader send OK
Changing bautrate OK.
Send Second Loader.
New flash metod detected.
UID: T1BF57_21_11_12
***************
Build ID: OPM2.171019.012
CPU arhitecture: armeabi-v7a
Manufacturer: ACE France
Hardware: sp9832e_1h10_go
Fota platform: Sprd9832_8.1
Build product name: AS0218
Build description: AS0218-user 8.1.0 OPM2.171019.012 90 release-keys
Product name: AS0218
Build Id: OPM2.171019.012
Model: BUZZ 1
Android Release: 8.1.0
Android Version: AS0218_V08_20181214
Security patch: 2018-12-05
This phone have frp partition.
CPU NAME: SC9832E
Removing frp, wait...
[0]FRP: persist
Format OK.
[can take 0-10 sec]Wait untill phone restart.
Exe version: NckBox Spreadtrum Module 2.2.0
Log saved:
C:\Users\fayca\Documents\spreadtrum_module\Saved_Logs\ACE_sp9832e_1h10_go_AS0218_V08_20181214_erase_frp.txt
Total Time: 00:00:18
Done.- إنضم
- 16 سبتمبر 2012
- المشاركات
- 3,612
- مستوى التفاعل
- 3,310
- النقاط
- 113
INFINIX Smart 5 (X657) FRP Reset
INFINIX Smart 5 (X657) FRP Reset
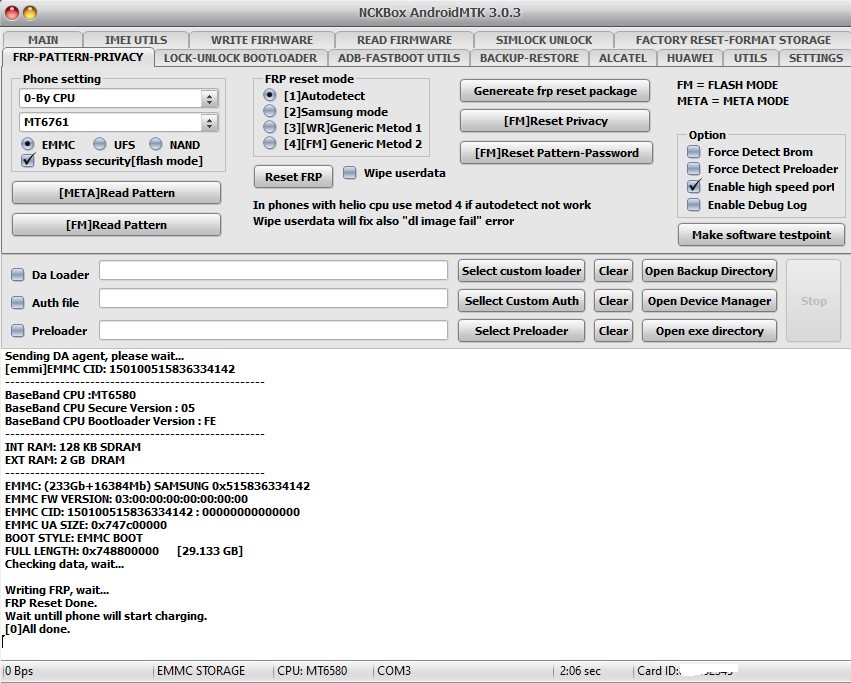
كود:
Exe version: NCKBox AndroidMTK 3.0.3 Selected model: 0-By CPU MT6761
[auto]Action: Reset FRP
Phone must be off with battery inside.
Battery must be charged
Please insert USB cable now...
Keep "VOL-" button untill inserting USB cable.
For some phones need to keep "VOL+ and VOL-" button untill inserting USB cable.
For some phones need to keep "VOL+" button untill inserting USB cable.
Detected(3) : MediaTek USB Port_V1633 (COM3)
[3] \\?\usb#vid_0e8d&pid_0003#5&2bccd040&0&1#{a5dcbf10-6530-11d2-901f-00c04fb951ed}
CPU: MT6580 CPU code: 6580 Target config: 5
***********************
Secure boot enabled: true
Need serial link authorization: false
Need download agent authorization: true
SWJTAG enabled: true
EPP_PARAM at 0x600 after EMMC_BOOT/SDMMC_BOOT: false
Root cert required: false
Memory read authorization: false
Memory write authorization: false
Cmd 0xC8 blocked: false
***********************
Executing exploit, do not disconnect phone
Exploit has been executed successfully.
[1e400]Dumping phone preloader.
Preloader: C:\ProgramData\Android_MTK_Backup_Folder\preloader_backup\preloader_x657_h8030.bin
Waiting for handle to become active......
Reseived active handle repply from phone......
Booting phone
Detected(3) : MediaTek USB Port_V1633 (COM3)
[3] \\?\usb#vid_0e8d&pid_0003#5&2bccd040&0&1#{a5dcbf10-6530-11d2-901f-00c04fb951ed}
Boot mode: Brom
BBCHIP: 6580 0 ca00
Using Algo 1.
Phone detected...Please wait
Sending DA agent, please wait...
[emmi]EMMC CID: 150100515836334142
----------------------------------------------------
BaseBand CPU :MT6580
BaseBand CPU Secure Version : 05
BaseBand CPU Bootloader Version : FE
----------------------------------------------------
INT RAM: 128 KB SDRAM
EXT RAM: 2 GB DRAM
----------------------------------------------------
EMMC: (233Gb+16384Mb) SAMSUNG 0x515836334142
EMMC FW VERSION: 03:00:00:00:00:00:00:00
EMMC CID: 150100515836334142 : 00000000000000
EMMC UA SIZE: 0x747c00000
BOOT STYLE: EMMC BOOT
FULL LENGTH: 0x748800000 [29.133 GB]
Checking data, wait...
Writing FRP, wait...
FRP Reset Done.
Wait untill phone will start charging.
[0]All done.- إنضم
- 16 سبتمبر 2012
- المشاركات
- 3,612
- مستوى التفاعل
- 3,310
- النقاط
- 113
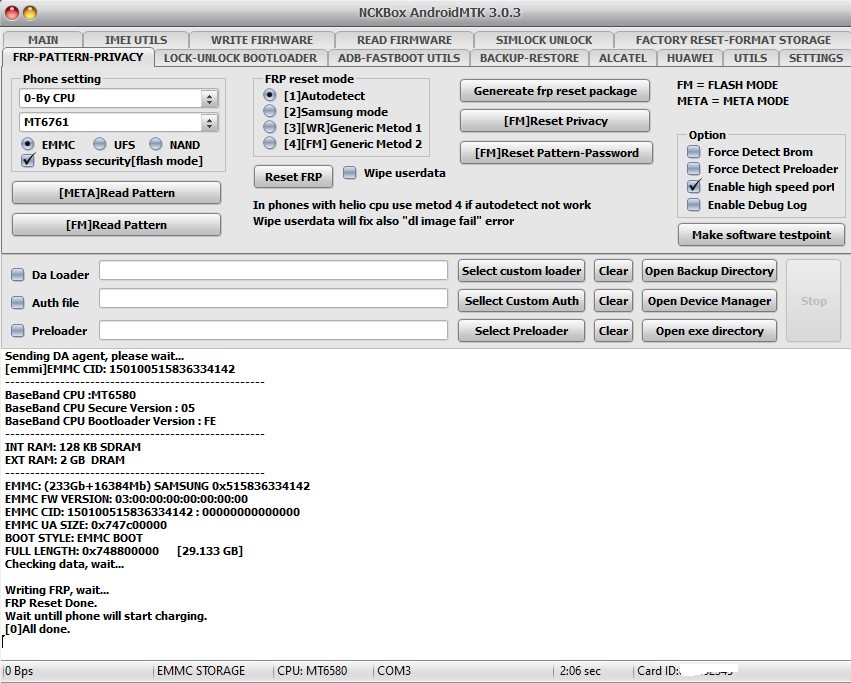
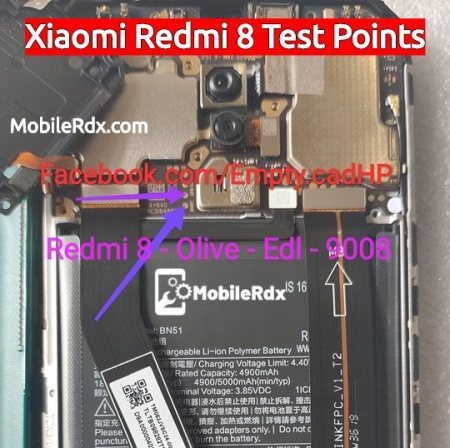
Xiaomi Redmi 8 FRP Reset Via Test Point
Xiaomi Redmi 8 FRP Reset Via Test Point
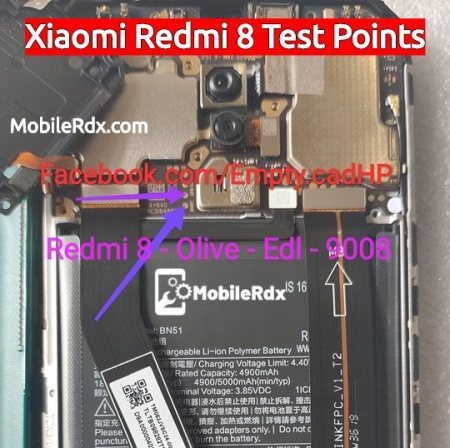
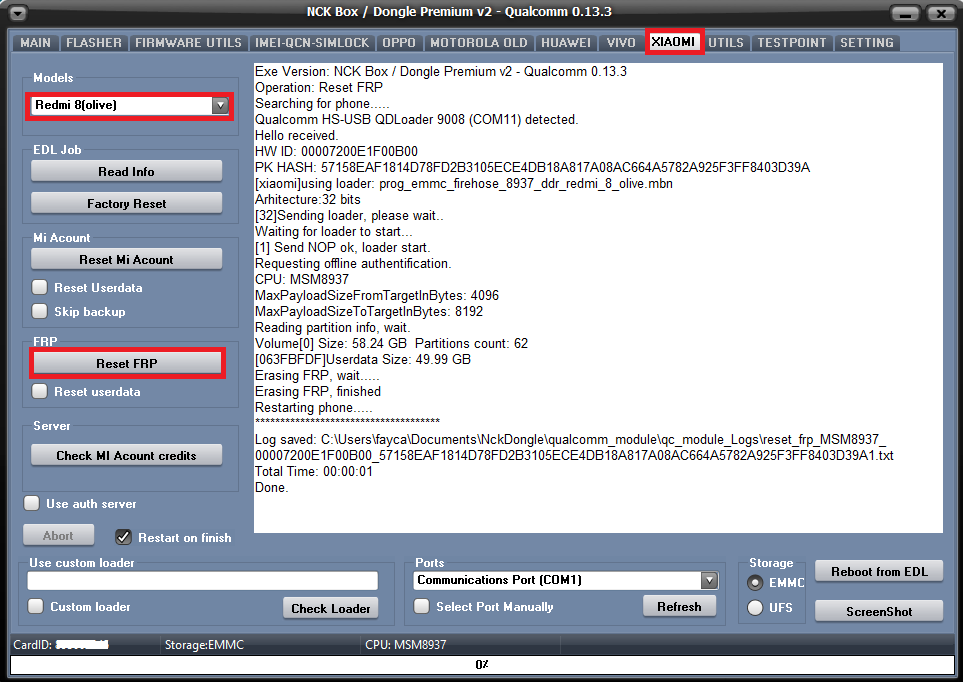
كود:
Exe Version: NCK Box / Dongle Premium v2 - Qualcomm 0.13.3Operation: Reset FRP
Searching for phone.....
Qualcomm HS-USB QDLoader 9008 (COM11) detected.
Hello received.
HW ID: 00007200E1F00B00
PK HASH: 57158EAF1814D78FD2B3105ECE4DB18A817A08AC664A5782A925F3FF8403D39A
[xiaomi]using loader: prog_emmc_firehose_8937_ddr_redmi_8_olive.mbn
Arhitecture:32 bits
[32]Sending loader, please wait..
Waiting for loader to start...
[1] Send NOP ok, loader start.
Requesting offline authentification.
CPU: MSM8937
MaxPayloadSizeFromTargetInBytes: 4096
MaxPayloadSizeToTargetInBytes: 8192
Reading partition info, wait.
Volume[0] Size: 58.24 GB Partitions count: 62
[063FBFDF]Userdata Size: 49.99 GB
Erasing FRP, wait.....
Erasing FRP, finished
Restarting phone.....
*************************************
Log saved: C:\Users\fayca\Documents\NckDongle\qualcomm_module\qc_module_Logs\reset_frp_MSM8937_00007200E1F00B00_57158EAF1814D78FD2B3105ECE4DB18A817A08AC664A5782A925F3FF8403D39A1.txt
Total Time: 00:00:01
Done.- إنضم
- 16 سبتمبر 2012
- المشاركات
- 3,612
- مستوى التفاعل
- 3,310
- النقاط
- 113
Samsung A10s (SM-107F) FRP Reset

كود:
Exe version: NCKBox AndroidMTK 3.0.3
Selected model: Samsung Galaxy A10S
[auto]Action: Reset FRP
Phone must be off with battery inside.
Battery must be charged
Please insert USB cable now...
Keep "VOL-" button untill inserting USB cable.
For some phones need to keep "VOL+ and VOL-" button untill inserting USB cable.
For some phones need to keep "VOL+" button untill inserting USB cable.
Detected(14) : MediaTek PreLoader USB VCOM_V1633 (Android) (COM14)
[14] \\?\usb#vid_0e8d&pid_2000#5&21e739f&0&3#{a5dcbf10-6530-11d2-901f-00c04fb951ed}
Switch preloader to bootrom...
crash succeed!
CPU: MT6765 CPU code: 766 Target config: e5
***********************
Secure boot enabled: true
Need serial link authorization: false
Need download agent authorization: true
SWJTAG enabled: true
EPP_PARAM at 0x600 after EMMC_BOOT/SDMMC_BOOT: false
Root cert required: false
Memory read authorization: true
Memory write authorization: true
Cmd 0xC8 blocked: true
***********************
Executing exploit, do not disconnect phone
Exploit has been executed successfully.
[3ea00]Dumping phone preloader.
Preloader: C:\ProgramData\Android_MTK_Backup_Folder\preloader_backup\preloader_s96116ca1.bin
Waiting for handle to become active......
Reseived active handle repply from phone......
Booting phone
Detected(4) : MediaTek USB Port_V1633 (COM4)
[4] \\?\usb#vid_0e8d&pid_0003#5&21e739f&0&3#{a5dcbf10-6530-11d2-901f-00c04fb951ed}
Boot mode: Brom
Phone detected...Please wait
BBCHIP: 6765 0 ca00
Using Algo 1.
Helio MT6765 phone detected, swithing to helio api
Helio enabled DRAM in First Da: FALSE
Sending loader.....
BBCHIP MT6765
[1]Storage EMMC
Block size: 512
EMMC FW VERSION: 00:00:00:00:00:00:00:00
EMMC CID: 15010051583633 : 000000000000000000
EMMC UA SIZE: 0x747c00000
BOOT STYLE: EMMC BOOT
FULL LENGTH: 0x749400000 [29.145 GB]
-Reading GPT Drive OK
[EMMC]FORMAT
[EMMC]FORMAT
[0]FRP Reset Done.
[helio]Wait untill phone will start charging.
[0]All done.- إنضم
- 16 سبتمبر 2012
- المشاركات
- 3,612
- مستوى التفاعل
- 3,310
- النقاط
- 113
كود:
SELECTED: Tiger T310(UMS312)
ACTION: Erase FRP
Start Detect phone...
Phone must be off with battery inside.
Long press "VOL -" key and insert usb cable.
For some phones need to
Long press "VOL -"+ "VOL +" key and insert usb cable.
Detected: SPRD U2S Diag (COM64)
Sending payload, keep boot key untill loader start.
Exploiting phone.....
Sending preloader 1
Sending preloader 2
Sending FDL 1.....
Sending FDL 2.....
New flash metod detected.
FileSystem: EMMC
Read partition info is supported by loader.
***************
[S]Manufacturer: DANEW
[S]Brand: DANEW
[S]Device: DANEW_Konnect_556
[S]Model: Konnect_556
Build ID: R01005
CPU arhitecture: armeabi-v7a
Build product name: S6B1
Build description: Konnect_556-user 11 R01005 1667787224 release-keys
Build Id: R01005
Android Release: 11
Android Version: S6B1_T64A_danew_k556_EBOT_E112_V01_221110
Security patch: 2022-10-05
CPU NAME: T310
Removing frp, wait...
[1]FRP: persist
Format OK.
[can take 0-10 sec]Wait untill phone restart.
Exe version: Unisoc Module 2.2.6
Log saved:
C:\nckdongle\spreadtrum_module\spreadtrum_module_backup_folder\Saved_Logs\DANEW_S6B1_T64A_danew_k556_EBOT_E112_V01_221110_erase_frp.txt
Total Time: 00:00:36
Done.- إنضم
- 16 سبتمبر 2012
- المشاركات
- 3,612
- مستوى التفاعل
- 3,310
- النقاط
- 113
كود:
Exe Version: NCK Box / Dongle Premium v2 - Qualcomm 0.13.5
Operation: [misc]Factory Format
How to connect phone:
1. With phone off enter edl mode keep pressing vol+ and vol- buttons and insert usb cable
2. If this metod not work, use edl cable to force emergenty download mode.
3. If this metod not work, use testpoint to force emergenty download mode.
Searching for phone.....
Qualcomm HS-USB QDLoader 9008 (COM63) detected.
Hello received.
HW ID: 65001500E1A00900 MSM8953
PK HASH: 6BC369511DA9CADB3A7AF61574F89DB385003D6241BDD1FF573DBA61BF6AE119
Checking database for suitable loader.....
Arhitecture:32 bits
[32]Sending loader, please wait..
Waiting for loader to start...
[0] Send NOP ok, loader start.
CPU: MSM8953
MaxPayloadSizeFromTargetInBytes: 4096
MaxPayloadSizeToTargetInBytes: 8192
Reading partition info, wait.
Volume[0] Size: 29.12 GB Partitions count: 57
[0310DFDF]Userdata Size: 24.53 GB
Resetting phone, wait.....
Resetting phone finished
Restarting phone.....
*************************************
Log saved: C:\Users\fayca\Documents\NckDongle\qualcomm_module\qc_module_Logs\misc_reset_userdata_MSM8953_65001500E1A00900_6BC369511DA9CADB3A7AF61574F89DB385003D6241BDD1FF573DBA61BF6AE1191.txt
Total Time: 00:00:03
Done.- إنضم
- 16 سبتمبر 2012
- المشاركات
- 3,612
- مستوى التفاعل
- 3,310
- النقاط
- 113
Xiaomi Redmi 10A (220233L2C) Reset FRP
كود:
[Reset FRP]
Waiting for device...Found
Port Info : MediaTek USB Port_V1633 (COM46) [\\?\usb#vid_0e8d&pid_0003#5&21e739f&0&3#{86e0d1e0-8089-11d0-9ce4-08003e301f73}]
: MediaTek Inc., 3.0.1504.0 [usb2ser.sys]
: BROM PORT
Hw ID : MT6765 [0766] Helio P35/G35
Details : 8A00,CA00,0000
Sec. Cfg : [SBA Active] [SLA Active] [DAA Active]
MEID : 074FF0E048B38CB24AFE38374642ABD7
SoC ID[0] : D901E3B406A92B31F5C1F260563150E1
SoC ID[1] : 6BCBB73321D1B99FBC03C0425042DA68
Executing Exploit...Done
Reading Preloader...OK
Saved as : preloader_k62v1_64_bsp.bin
Loading EMI Config from Preloader...OK
Sec. Cfg : [SBA Inactive] [SLA Inactive] [DAA Inactive]
Sending DA1...OK
Running DA1...OK
Waiting DA SYNC Signal...OK
Setting Checksum Level...Done [Storage]
Connection : brom
Speed : HIGH-SPEED
Reading EMI Configuration...OK
EMMC CID : 9B0100593250303634002A09449B5901
Sending EMI Config...OK
Sending 2nd DA...OK
Activating DA Extension...OK
Int. RAM : 0x0000000000038000 [224.00 KB]
Ext. RAM : 0x0000000100000000 [4.00 GB]
Flash ID : Y2P064
CID : 9B0100593250303634002A09449B5901
BOOT1 : 0x0000000000400000 [4.00 MB]
BOOT2 : 0x0000000000400000 [4.00 MB]
RPMB : 0x0000000001000000 [16.00 MB]
USERAREA : 0x0000000E8F800000 [58.24 GB]
Reading Parititon Info...OK
Manufacturer : Xiaomi
And. Ver. : 11
Build Dt. : Tue Apr 26 21:53:26 CST 2022
Display ID : RP1A.200720.011
Ver. Inc. : V12.5.5.0.RCZMIXM
Locale : en-GB
Mod. Dev. : dandelion_c3l2_global
Patch : 2022-04-01
Reset FRP Data...Done
Process finished
[NCK MTK Exploit Tool v1.0]
LOG TXT : 20240127_153639.txt- إنضم
- 16 سبتمبر 2012
- المشاركات
- 3,612
- مستوى التفاعل
- 3,310
- النقاط
- 113
كود:
SELECTED: SM-A032F
ACTION: Erase FRP
Start Detect phone.
Testpoint image link for this model is located in utils tab
Phone must be off(you can service this phone without battery also).
Connect Testpoint while inserting usb cable.
After booting, testpoint can be removed.
Detected: SPRD U2S Diag (COM92)
Sending payload, keep boot key untill loader start.
Exploiting phone.....
Sending preloader 1
Sending preloader 2
Sending FDL 1.....
Sending FDL 2.....
New flash metod detected.
FileSystem: EMMC
Read partition info is supported by loader.
***************
[S]Manufacturer: samsung
[S]Brand: samsung
[S]Device: a3core
[S]Model: SM-A032F
Build ID: RP1A.201005.001
CPU arhitecture: armeabi-v7a
Build product name: a3core
Build description: a3corexx-user 11 RP1A.201005.001 A032FXXU1AUL5 release-keys
Build Id: RP1A.201005.001
Android Release: 11
Android Version: RP1A.201005.001.A032FXXU1AUL5
Security patch: 2021-12-01
CPU NAME: SC9863A
Removing frp, wait...
Found [persistent] [persistent] Size to download: 1024 KB
[1]FRP: persistent
Format OK.
[can take 0-10 sec]Wait untill phone restart.
Exe version: Unisoc Module 2.2.8
Log saved:
C:\nckdongle\spreadtrum_module\spreadtrum_module_backup_folder\Saved_Logs\samsung_RP1A_201005_001_A032FXXU1AUL5_erase_frp.txt
Total Time: 00:00:41
Done.- إنضم
- 16 سبتمبر 2012
- المشاركات
- 3,612
- مستوى التفاعل
- 3,310
- النقاط
- 113
كود:
[Userdata + FRP]
Waiting for device...Found
Port Info : MediaTek USB Port_V1633 (COM46) [\\?\usb#vid_0e8d&pid_0003#5&21e739f&0&3#{f9f3ff14-ae21-48a0-8a25-8011a7a931d9}]
: MediaTek Inc., 3.0.1504.0 [usb2ser.sys]
: BROM PORT
Hw ID : MT6765 [0766] Helio P35/G35
Details : 8A00,CA00,0000
Sec. Cfg : [SBA Active] [SLA Inactive] [DAA Active]
MEID : D5059A1A6B236E75782E0DB6B4F6FF1D
SoC ID[0] : 3B46EBBAA44BA820FF43425C67FD1DA3
SoC ID[1] : 7B00CC3BAE7FB9E3AF6D8977B8CEF19E
Executing Exploit...Done
Reading Preloader...OK
Saved as : preloader_oppo6765.bin
Loading EMI Config from Preloader...OK
Sec. Cfg : [SBA Inactive] [SLA Inactive] [DAA Inactive]
Sending DA1...OK
Running DA1...OK
Waiting DA SYNC Signal...OK
Setting Checksum Level...Done [Storage]
Connection : brom
Speed : HIGH-SPEED
Reading EMI Configuration...OK
EMMC CID : 90014A68423861503E03004C3438583F
Sending EMI Config...OK
Sending 2nd DA...OK
Activating DA Extension...OK
Int. RAM : 0x0000000000038000 [224.00 KB]
Ext. RAM : 0x00000000C0000000 [3.00 GB]
Flash ID : hB8aP>
CID : 90014A68423861503E03004C3438583F
BOOT1 : 0x0000000000400000 [4.00 MB]
BOOT2 : 0x0000000000400000 [4.00 MB]
RPMB : 0x0000000001000000 [16.00 MB]
USERAREA : 0x0000000747C00000 [29.12 GB]
Reading Parititon Info...OK
And. Ver. : 10
Build Dt. : Wed Apr 26 14:39:43 CST 2023
Display ID : QP1A.190711.020 release-keys
Locale : en-US
Patch : 2023-02-05
Formating Userdata...Done
Reset FRP Data...Done
Process finished
[NCK MTK Exploit Tool v1.0]
LOG TXT : 20240130_174044.txt
Screenshot : Screenshot_24-01-30-174155- إنضم
- 16 سبتمبر 2012
- المشاركات
- 3,612
- مستوى التفاعل
- 3,310
- النقاط
- 113
كود:
[Reset FRP]
Waiting for device...Found
Port Info : MediaTek USB Port_V1633 (COM46) [\\?\usb#vid_0e8d&pid_0003#5&21e739f&0&3#{86e0d1e0-8089-11d0-9ce4-08003e301f73}]
: MediaTek Inc., 3.0.1504.0 [usb2ser.sys]
: BROM PORT
Hw ID : MT6768 [0707] Helio P65/G85 k68v1
Details : 8A00,CA00,0000
Sec. Cfg : [SBA Active] [SLA Active] [DAA Active]
MEID : 172BB6DD4AF29E9858EEDC4BEDF663B8
SoC ID[0] : 442FD36AB63D6C4AB0385C77566C85BA
SoC ID[1] : E94D4DEAA44787692C68F678E96DB477
Executing Exploit...Done
Reading Preloader...OK
Saved as : preloader_lancelot.bin
Loading EMI Config from Preloader...OK
Sec. Cfg : [SBA Inactive] [SLA Inactive] [DAA Inactive]
Sending DA1...OK
Running DA1...OK
Waiting DA SYNC Signal...OK
Setting Checksum Level...Done [Storage]
Connection : brom
Speed : HIGH-SPEED
Reading EMI Configuration...OK
EMMC CID : 150100445036444142035545D46348E9
Sending EMI Config...OK
Sending 2nd DA...OK
Activating DA Extension...OK
Int. RAM : 0x0000000000070000 [448.00 KB]
Ext. RAM : 0x0000000100000000 [4.00 GB]
Flash ID : DP6DAB
CID : 150100445036444142035545D46348E9
BOOT1 : 0x0000000000400000 [4.00 MB]
BOOT2 : 0x0000000000400000 [4.00 MB]
RPMB : 0x0000000001000000 [16.00 MB]
USERAREA : 0x0000000E8F800000 [58.24 GB]
Reading Parititon Info...OK
Manufacturer : Xiaomi
And. Ver. : 11
Build Dt. : Wed Jun 9 20:30:33 CST 2021
Display ID : RP1A.200720.011
Ver. Inc. : V12.0.1.0.RJCMIXM
Locale : en-GB
Mod. Dev. : lancelot_global
Patch : 2021-05-01
Reset FRP Data...Done
Process finished
[NCK MTK Exploit Tool v1.0]
LOG TXT : 20240203_140332.txt- إنضم
- 16 سبتمبر 2012
- المشاركات
- 3,612
- مستوى التفاعل
- 3,310
- النقاط
- 113
كود:
[Reset FRP]
Waiting for device...Found
Port Info : MediaTek USB Port_V1633 (COM46) [\\?\usb#vid_0e8d&pid_0003#5&21e739f&0&3#{86e0d1e0-8089-11d0-9ce4-08003e301f73}]
: MediaTek Inc., 3.0.1504.0 [usb2ser.sys]
: BROM PORT
Hw ID : MT6765 [0766] Helio P35/G35
Details : 8A00,CA00,0000
Sec. Cfg : [SBA Active] [SLA Active] [DAA Active]
MEID : 154A6EA50B1B60BCAE3ED2F319C7464A
SoC ID[0] : BABE0FF11C7EBF835033841F75F69744
SoC ID[1] : BF4E2353B129F624E91EB32EED98891B
Executing Exploit...Done
Reading Preloader...OK
Saved as : preloader_k62v1_64_bsp.bin
Loading EMI Config from Preloader...OK
Sec. Cfg : [SBA Inactive] [SLA Inactive] [DAA Inactive]
Sending DA1...OK
Running DA1...OK
Waiting DA SYNC Signal...OK
Setting Checksum Level...Done [Storage]
Connection : brom
Speed : HIGH-SPEED
Reading EMI Configuration...OK
EMMC CID : 9B010059325030333200744009FF7819
Sending EMI Config...OK
Sending 2nd DA...OK
Activating DA Extension...OK
Int. RAM : 0x0000000000038000 [224.00 KB]
Ext. RAM : 0x0000000080000000 [2.00 GB]
Flash ID : Y2P032
CID : 9B010059325030333200744009FF7819
BOOT1 : 0x0000000000400000 [4.00 MB]
BOOT2 : 0x0000000000400000 [4.00 MB]
RPMB : 0x0000000001000000 [16.00 MB]
USERAREA : 0x0000000747C00000 [29.12 GB]
Reading Parititon Info...OK
Manufacturer : Xiaomi
And. Ver. : 10
Build Dt. : Thu Jul 1 13:04:39 CST 2021
Display ID : QP1A.190711.020
Ver. Inc. : V12.0.15.0.QCDMIXM
Locale : en-GB
Mod. Dev. : dandelion_global
Patch : 2021-06-01
Reset FRP Data...Done
Process finished
[NCK MTK Exploit Tool v1.0]
LOG TXT : 20240207_152016.txt- إنضم
- 16 سبتمبر 2012
- المشاركات
- 3,612
- مستوى التفاعل
- 3,310
- النقاط
- 113
كود:
[Reset FRP]
Waiting for device...Found
Port Info : MediaTek USB Port_V1633 (COM46) [\\?\usb#vid_0e8d&pid_0003#5&21e739f&0&3#{86e0d1e0-8089-11d0-9ce4-08003e301f73}]
: MediaTek Inc., 3.0.1504.0 [usb2ser.sys]
: BROM PORT
Hw ID : MT6765 [0766] Helio P35/G35
Details : 8A00,CA00,0000
Sec. Cfg : [SBA Active] [SLA Inactive] [DAA Active]
MEID : E2DF074499D954605CF7A3AE987FC9FB
SoC ID[0] : 87B1133BDA23762B001AC293436B97A8
SoC ID[1] : 51AA809A48F246B573BE3456A5F0FED9
Executing Exploit...Done
Reading Preloader...OK
Saved as : preloader_amar_row_wifi.bin
Loading EMI Config from Preloader...OK
Sec. Cfg : [SBA Inactive] [SLA Inactive] [DAA Inactive]
Sending DA1...OK
Running DA1...OK
Waiting DA SYNC Signal...OK
Setting Checksum Level...Done [Storage]
Connection : brom
Speed : HIGH-SPEED
Reading EMI Configuration...OK
EMMC CID : 1501003458364B4D42036B79DC189891
Sending EMI Config...OK
Sending 2nd DA...OK
Activating DA Extension...OK
Int. RAM : 0x0000000000038000 [224.00 KB]
Ext. RAM : 0x0000000080000000 [2.00 GB]
Flash ID : 4X6KMB
CID : 1501003458364B4D42036B79DC189891
BOOT1 : 0x0000000000400000 [4.00 MB]
BOOT2 : 0x0000000000400000 [4.00 MB]
RPMB : 0x0000000000400000 [4.00 MB]
USERAREA : 0x0000000747C00000 [29.12 GB]
Reading Parititon Info...OK
And. Ver. : 10
Build Dt. : Thu Jun 30 02:45:43 CST 2022
Display ID : TB-X306F_S120388_220630_BMP
Ver. Inc. : TB-X306F_USR_S120388_2206300015_V9.48_BMP_ROW
Patch : 2022-07-05
Reset FRP Data...Done
Process finished
[NCK MTK Exploit Tool v1.0]
LOG TXT : 20240208_132533.txt- إنضم
- 16 سبتمبر 2012
- المشاركات
- 3,612
- مستوى التفاعل
- 3,310
- النقاط
- 113
كود:
[Userdata + FRP]
Waiting for device...Found
Port Info : MediaTek USB Port_V1633 (COM46) [\\?\usb#vid_0e8d&pid_0003#5&21e739f&0&3#{86e0d1e0-8089-11d0-9ce4-08003e301f73}]
: MediaTek Inc., 3.0.1504.0 [usb2ser.sys]
: BROM PORT
Hw ID : MT6761 [0717] Helio A20/P22/A22/A25/G25
Details : 8A00,CA01,0200
Sec. Cfg : [SBA Active] [SLA Active] [DAA Active]
MEID : 1860A223C22C3D1EC012AE06F358AB85
SoC ID[0] : AA41594DA83025ED271DAB3EFAD5E7DC
SoC ID[1] : 39D45CAED4700D8CC52476BABE597779
Executing Exploit...Done
Reading Preloader...OK
Saved as : preloader_ice.bin
Loading EMI Config from Preloader...OK
Sec. Cfg : [SBA Inactive] [SLA Inactive] [DAA Inactive]
Sending DA1...OK
Running DA1...OK
Waiting DA SYNC Signal...OK
Setting Checksum Level...Done [Storage]
Connection : brom
Speed : HIGH-SPEED
Reading EMI Configuration...OK
EMMC CID : 9B010059325030333200913938BA7933
Sending EMI Config...OK
Sending 2nd DA...OK
Activating DA Extension...OK
Int. RAM : 0x0000000000039000 [228.00 KB]
Ext. RAM : 0x0000000080000000 [2.00 GB]
Flash ID : Y2P032
CID : 9B010059325030333200913938BA7933
BOOT1 : 0x0000000000400000 [4.00 MB]
BOOT2 : 0x0000000000400000 [4.00 MB]
RPMB : 0x0000000001000000 [16.00 MB]
USERAREA : 0x0000000747C00000 [29.12 GB]
Reading Parititon Info...OK
Formating Userdata...Done
Reset FRP Data...Done
Process finished
[NCK MTK Exploit Tool v1.0]
LOG TXT : 20240212_102609.txtالمرفقات
- إنضم
- 16 سبتمبر 2012
- المشاركات
- 3,612
- مستوى التفاعل
- 3,310
- النقاط
- 113
Alcatel Onetouch Pixi 4 (5) (5045D) Reset FRP
كود:
Exe version: NCKBox AndroidMTK 3.0.3
Selected model: Alcatel OT-5045D
[auto]Action: Reset FRP
Keep "VOL-" button untill inserting USB cable.
For some phones need to keep "VOL+ and VOL-" button untill inserting USB cable.
For some phones need to keep "VOL+" button untill inserting USB cable.
Detected(14) : MediaTek PreLoader USB VCOM_V1633 (Android) (COM14)
[14] \\?\usb#vid_0e8d&pid_2000#5&21e739f&0&3#{a5dcbf10-6530-11d2-901f-00c04fb951ed}
Boot mode: Preloader
BBCHIP: 335 0 ca00
Using Algo 2.
Phone detected...Please wait
Sending DA agent, please wait...
----------------------------------------------------
BaseBand CPU :MT6735M
BaseBand CPU Secure Version : FF
BaseBand CPU Bootloader Version : 01
----------------------------------------------------
INT RAM: 128 KB SDRAM
EXT RAM: 1 GB DRAM
----------------------------------------------------
EMMC: (58Gb+8192Mb) MICRON 0x50314a39354b
EMMC FW VERSION: 12:00:00:00:00:00:00:00
EMMC CID: FE014E50314A39354B : 00000000000000
EMMC UA SIZE: 0x1d3000000
BOOT STYLE: EMMC BOOT
FULL LENGTH: 0x1d3600000 [7.303 GB]
Checking data, wait...
Writing FRP, wait...
FRP Reset Done.
Wait untill phone will start charging.
[0]All done.- إنضم
- 16 سبتمبر 2012
- المشاركات
- 3,612
- مستوى التفاعل
- 3,310
- النقاط
- 113
كود:
[Reset FRP]
Waiting for device...Found
Port Info : MediaTek PreLoader USB VCOM_V1633 (Android) (COM59) [\\?\usb#vid_22d9&pid_0006#5&21e739f&0&3#{86e0d1e0-8089-11d0-9ce4-08003e301f73}]
: MediaTek Inc., 3.0.1504.0 [usb2ser.sys]
: PRELOADER PORT
Preloader port found, need BROM!
Trying to crash preloader...OK
Hw ID : MT6765 [0766] Helio P35/G35
Details : 8A00,CA00,0000
Sec. Cfg : [SBA Active] [SLA Inactive] [DAA Active]
MEID : 8A9B74E1F240658476B2BC20B8DF9EFC
SoC ID[0] : A4998A44A3619098014B83828A865178
SoC ID[1] : 889B0A7C692B24F6E9EB856DE43559DC
Executing Exploit...Done
Reading Preloader...OK
Saved as : preloader_k65v1_64_bsp.bin
Loading EMI Config from Preloader...OK
Sec. Cfg : [SBA Inactive] [SLA Inactive] [DAA Inactive]
Sending DA1...OK
Running DA1...OK
Waiting DA SYNC Signal...OK
Setting Checksum Level...Done [Storage]
Connection : brom
Speed : HIGH-SPEED
Reading EMI Configuration...OK
EMMC CID : 15010044555442343202400F533F4A6D
Sending EMI Config...OK
Sending 2nd DA...OK
Activating DA Extension...OK
Int. RAM : 0x0000000000038000 [224.00 KB]
Ext. RAM : 0x0000000100000000 [4.00 GB]
Flash ID : DUTB42
CID : 15010044555442343202400F533F4A6D
BOOT1 : 0x0000000000400000 [4.00 MB]
BOOT2 : 0x0000000000400000 [4.00 MB]
RPMB : 0x0000000001000000 [16.00 MB]
USERAREA : 0x0000001D1EC00000 [116.48 GB]
Reading Parititon Info...OK
Reset FRP Data...Done
Process finished
[NCK MTK Exploit Tool v1.0]
LOG TXT : 20240220_173541.txt